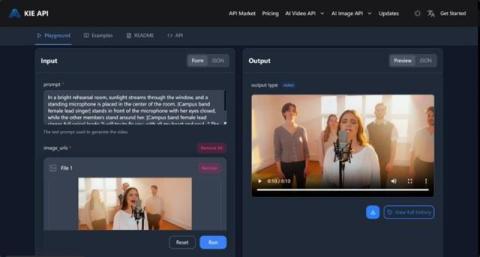
Kling Video 2.6 API: How to Build Automated Visual Simulation Workflows
The landscape of generative media has shifted from simple prompt-based experimentation to sophisticated, integrated production pipelines. With the release of Kling 2.6, the focus has moved toward "Native Audio-Visual Generation"-a breakthrough that allows developers to synchronize high-fidelity visuals with context-aware sound in a single automated step. For platforms focusing on digital senses and technical security, the Kling Video 2.6 API offers a robust framework for building simulations that were previously too resource-intensive to automate.