Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Vulnerability assessment identifies weaknesses or vulnerabilities in computer systems, networks, and software, along with the inherent risks they introduce. By using specialized tools like vulnerability scanners and manual methods, vulnerability assessment helps organizations figure out where they might be at risk. This process not only identifies potential problems but also helps prioritize them based on their severity level.
Securely implementing Active Directory on Windows Server 2019
The installation of Active Directory (AD) on Windows Server 2019 calls for a thorough understanding of technical nuances and a steadfast dedication to security best practices. This guide will walk you through the process of securely implementing Active Directory, ensuring the highest level of protection for the information and resources within your company.
Takeaways and Observations from Black Hat USA 2023, BSides, and DEFCON 31
As happens every year, Netskopers from across different teams attended the Black Hat USA, BSides, and DEFCON conferences, each coming away with their own take on what was new and exciting. With “Summer Camp” now behind us, we checked in with those folks who attended to share some of what they saw on the floor and what exciting topics stuck out most to them. Here’s what they had to say.
8 Key Elements of a Third-Party Risk Management Policy
Any organization that relies on third-party vendors for critical business functions should develop and maintain an effective third-party risk management (TPRM) policy. A TPRM policy is the first document an organization should create when establishing its TPRM program. TPRM policies allow organizations to document internal roles and responsibilities, develop regulatory practices, and appropriately communicate guidelines to navigate third-party risks throughout the vendor lifecycle.
Choosing an External Attack Surface Management Tool (in 2023)
The external attack surface is the sum of all potential attack vectors originating outside your internal network, that is, your third-party attack surface. With reliance on third-party vendor relationships increasing, External Attack Surface Management (EASM) plays a more prominent role in data breach prevention programs.
Key Steps to Developing an Effective Third-Party Risk Management Program
A Third-Party Risk Management Program (TPRM) is a systematic approach to mitigating risks associated with third parties, such as vendors, suppliers, and contractors. It includes an assessment process that identifies, evaluates, and remediates any risks affecting your organization. Implementing effective third-party risk management (TPRM) measures can safeguard organizations against potential threats and promote seamless and confident collaborations with external partners.
What is the Computer Fraud and Abuse Act (CFAA)?
The U.S. Federal Government passed the Computer Fraud and Abuse Act (18 U.S.C.§1030) (CFAA) in 1986 as an amendment to the Comprehensive Crime Control Act of 1984, which included the first federal computer crime statute. Since enacting the CFAA, congress and the federal government have amended the act multiple times to extend its reach and impose criminal and civil liability on additional malicious computer activities.
Choosing Automated Risk Remediation Software (in 2023)
When it comes to improving your cybersecurity posture, few strategies have as much of an impact as your cyber risk remediation program. Efficient risk remediation ensures security risks and vulnerabilities are shut down faster, reducing the potential risks of data breaches and their financial impacts. The cornerstone of an efficient remediation program is cyber risk remediation software that automates manual processes to improve the efficacy of risk mitigation efforts.
Application Security Requirements: Trends and Best Practices
Ensuring application security is not just about protecting data. It’s about safeguarding your company's reputation, keeping customer trust, and adhering to increasingly stringent regulatory requirements. Read on as we delve into application security requirements: the pressing security threats impacting applications, the critical security requirements your application needs to meet, and the best practices to adopt to achieve robust application security.
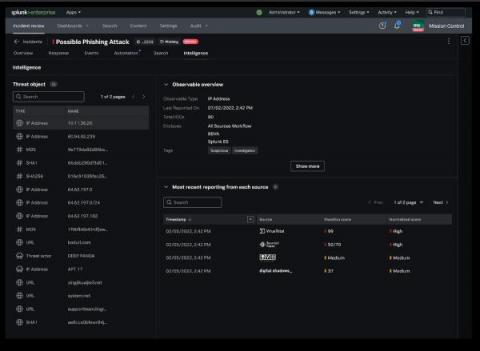
Integrated Intelligence Enrichment With Threat Intelligence Management
SOC analysts are overwhelmed with alerts and manual repetitive tasks that negatively impact their ability to conduct and prioritize investigations of critical events. They don’t have the time, or bandwidth, to sift through data feeds or sources to identify and synthesize intelligence related to an incident.