Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Spring4Shell: The zero-day RCE in the Spring Framework explained
On March 30, 2022, a critical remote code execution (RCE) vulnerability was found in the Spring Framework. More specifically, it is part of the spring-beans package, a transitive dependency in both spring-webmvc and spring-webflux. This vulnerability is another example of why securing the software supply chain is important to open source.
RDS Clipboard Redirection: Should you allow it?
The Essential List of Terraform Modules and Their Purposes
Rapid and constantly-evolving software development cycles have increased the need for reliable and fast infrastructure changes. Thus manually carrying out infrastructure changes has become an unscalable process – which is what Infrastructure as Code (IaC) tools are here to solve. They enable teams to codify their infrastructure configurations and integrate them directly into their CI/CD pipelines.
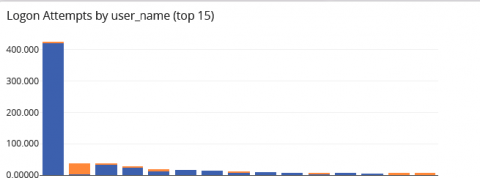
Building Your Security Analytics Use Cases
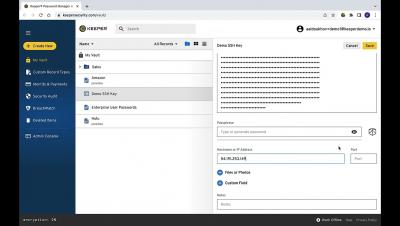
Keeper Commander - Using SSH Command
This Week in VulnDB - highlight on sprint4shell and dep supply chain vulnerability
Using the Snyk Vulnerability Database to find projects for The Big Fix
As developers, we all have our morning startup routine: make coffee, check Slack/Discord/email, read the latest news. One thing I do as part of my daily startup routine is check the Snyk Vulnerability Database for the latest open source vulnerabilities. It’s been especially interesting to see the types of exploits and vulnerabilities that appear in different ecosystems.
The Cloud Expansion Checklist: How to Get IT Decision-Makers and Developers on the Same Page
Cloud-native and open-source technologies are booming. But for a successful cloud expansion, IT decision-makers and developers need to be in agreement despite their unique roles in the process. As more enterprises transition to cloud-native environments, the big question is how aligned are IT decision-makers and developers?
Is there such a thing as Spring4Shell?
Very early in the morning on March 30th (for me), my colleague DeveloperSteve posted a “Hey, have you seen this?” message in our slack channel. It was an “advance warning” of a “probable” remote code execution (RCE) in the massively popular Java Spring framework. I would come to find out that even earlier than that, the Snyk Security team started investigation a potential RCE in Spring after seeing a tweet that has since been deleted.