Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The Rise of APIs: Data Integration & Microservices #APIGrowth #Microservices #DataIntegration
Navigating the Evolution: A Tactical Guide to Monolithic to Microservices Transformation
How to improve your microservices architecture security
How to Secure a Service Mesh Architecture
Many organizations build applications using microservices that often communicate with other distributed services. Ensuring that they remain secure requires a “secure token service,” secure communication protocols (mTLS), authentication, authorization, and data encryption.
How to secure microservices in a Zero-Trust environment
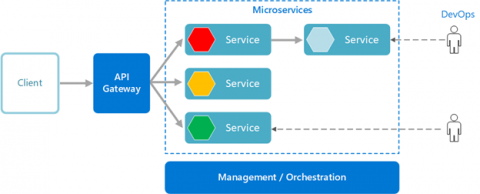
Microservices architecture is a convenient way to silo different software services compared to traditional software architecture and design. However, with multiple microservices communicating amongst each other - the attack surface of the network is greatly increased. The security of such a system depends on the security of all the services. Any deviation in the system’s security ultimately undermines the integrity of the entire network.
Testing Microservice Architectures
Mapping vulnerabilities to microservices with Snyk and OpsLevel
John Laban is the Founder & CEO at OpsLevel. This blog post originally appeared on the OpsLevel blog. Snyk is rapidly becoming the de facto standard for businesses that want to build security into their continuous software development processes. And with their developer-first tooling and best-in-class security intelligence, it’s no surprise.
Snyk Container meets Cloud Native Buildpacks: Cloud Native Application Security the right way
So you’re running microservices in containers? Congratulations! This is an important step towards meeting those business needs around delivering applications to the hands of your customers as soon as possible. But how can we mitigate any potential risks associated with faster software deployment? Simple, with Snyk.