Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Recent Cyber Attacks - 2023
The prediction is that $8 trillion will be lost to cyber crimes by the end of 2023, which is almost a third of the USA’s GDP in 2022 and twice as much as India’s predicted GDP in March 2023. The global loss to cybercrime is will grow more than 15% year by year to reach $10.5 trillion by 2025.
What is a Cross-Site Request Forgery (CSRF) Attack?
Successful hackers have the ability to find a specific vulnerability and turn it into millions of dollars if the account is large enough. Good hackers keep it simple by using the browser as a means to attack unwitting users. Cross-site request forgery, commonly called CSRF, is an innovative attack method in which hackers use header and form data to exploit the trust a website has in a user’s browser.
What Is a DMA Attack? Understanding and Mitigating the Threat
You have probably wondered what would happen if your company laptop got lost or stolen. Would someone be able to extract sensitive data from your laptop even if the device is encrypted or locked? There are several ways to compromise a laptop with physical access, and one of them is through a direct memory access (DMA) attack.
Protecting Nonprofits From Cyber Attacks
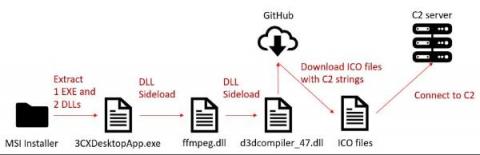
How to Detect and Mitigate the 3CXDesktopApp Supply Chain Attack
On March 29, researchers from two security companies identified an active campaign originating from a modified version of a legitimate, signed application: 3CXDesktopApp, a popular voice and video conferencing software. 3CXDesktopApp is developed by 3CX, a business communications software company. According to its website, 3CX has 600,000 client organizations and 12 million daily users.
SQL INJECTION ATTACK
The New Frontiers of Cybersecurity - Exponential Increase in Complexity
The New Frontiers of Cybersecurity is a three-part thought-leadership series investigating the big-picture problems within the cybersecurity industry. In the first post, we explored the reasons malicious actors have been able to enhance their ability to execute and profit from attacks. In the second post, we discussed how the massive increase in endpoints and systems online has dramatically increased the attack surface.
A State of Siege: Cyberattacks Soar Across the UK and Ireland
Organisations across the UK and Ireland must take precautions to protect their systems to reduce their risk of cyberattack.
Chinese fraudsters: evading detection and monetizing stolen credit card information
Cyber attacks are common occurrences that often make headlines, but the leakage of personal information, particularly credit card data, can have severe consequences for individuals. It is essential to understand the techniques employed by cyber criminals to steal this sensitive information.