Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Buying AI Tools? How to Cut Through Buzzwords
Buzzwords can’t protect you from liability. If you buy something because it sounds smart but can’t perform, that’s on you. Buying AI Tools? How to Cut Through Buzzwords.
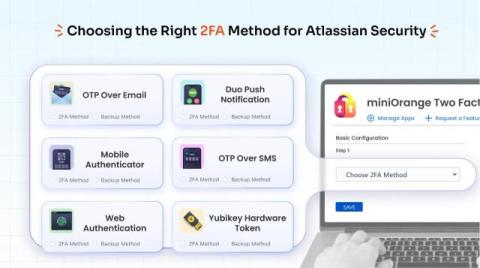
SMS, Email, TOTP or Push? How to Choose the Right 2FA Method for Your Atlassian Users
Choosing the right multi-factor authentication (MFA) method can be a tricky decision for Atlassian admins. With options like SMS, Email, TOTP, and Push notifications, each comes with its own benefits and trade-offs. Let’s understand the strengths and weaknesses of different MFA methods.
Multi-Tenant Systems: Sharing Vulnerabilities #appsec
Mend.io, formerly known as Whitesource, has over a decade of experience helping global organizations build world-class AppSec programs that reduce risk and accelerate development -– using tools built into the technologies that software and security teams already love. Our automated technology protects organizations from supply chain and malicious package attacks, vulnerabilities in open source and custom code, and open-source license risks.
The Role of Behavioral Machine Learning in Detecting Network Anomalies at Scale
Enterprise networks face a fundamental challenge: traditional signature-based detection methods fail against sophisticated threats that deliberately mimic legitimate traffic patterns. With networks generating terabytes of data daily and attack surfaces expanding through digital transformation, organizations need detection mechanisms that can identify subtle behavioral deviations without relying on known attack signatures.
Where Online Analytical Processing (OLAP) Overlaps With Security Operations
Imagine security data and analytics like a carnival’s hall of mirrors. From convex mirrors that show you a shorter, squatter version of something to the concave mirrors that show a highly magnified image, you see the same object in multiple ways. Every view gives you a different insight and provides a unique vantage point. Online Analytical Processing (OLAP) systems are different mirrors that allow security teams to create focused analytics models for different insights about your security posture.
How to Install the Aurora Protect Agent on Windows
In this video, we'll demonstrate how easy it is to install the Aurora Protect agent on a Windows system, then validate the successful install in the Aurora Console.
How Arctic Wolf Managed Risk Helps Organizations Discover, Assess and Secure Assets
Using two different use cases, this video will demonstrate how the Assets page helps Arctic Wolf Managed Risk customers assess assets, identify risks, prioritize mitigations and work towards ending cyber risk.
Defeating Ransomware with Unified Security
Ransomware is getting smarter, so your security better be, too. The old playbook of scattered tools and siloed defenses no longer cuts it. Every business needs to connect the dots to stay ahead. In this webinar, we’ll show you how bringing together SASE, XDR, NDR, and automation under a unified platform creates a powerful security force that works with your team, not against it.
Sharing Passwords via Email? What You Should Do Instead.
Emails are unencrypted, easily intercepted and impossible to recall. Learn more about why sharing passwords via email is an insecure practice and what you should do instead.