Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
KlusterKit - Enable Kubernetes based Architectures in Air Gapped Deployments
Early adopter enterprises across verticals such as Retail, Manufacturing, Oil & Gas are looking to incorporate containers and Kubernetes as a way of modernizing their applications. Choosing k8s as a standard ensures that these applications can be deployed these on different data center infrastructures (bare metal/VMware/KVM on OpenStack etc) or on public clouds (AWS/Azure/GCP etc).
Hunting for Linux library injection with Osquery
When analyzing malware and adversary activity in Windows environments, DLL injection techniques are commonly used, and there are plenty of resources on how to detect these activities. When it comes to Linux, this is less commonly seen in the wild. I recently came across a great blog from TrustedSec that describes a few techniques and tools that can be used to do library injection in Linux.
10 Best SIEM Use Cases (Part 1)
Due to the sheer scale of challenges cybersecurity threats pose today, an enterprise-level security solution is always necessary for organizations. Is your company facing too many false positives? Are you spending too much time and budget on your corporate cybersecurity posture? Are you worried about vulnerable protocols and misconfigurations? Don’t worry!
Cyber Security Challenges in Healthcare IoT Devices
The recent Vectra 2019 Spotlight Report on Healthcare indicates that the proliferation of healthcare internet-of-things (IoT) devices, along with a lack of network segmentation, insufficient access controls and reliance on legacy systems, has created an increasing attack surface that can be exploited by cyber criminals determined to steal personally identifiable information (PII) and protected health information (PHI) in addition to disrupt healthcare delivery processes.
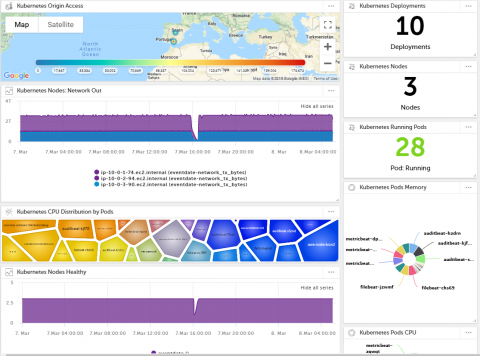
Introducing Devo Activeboards: A New Way to Visualize Machine Data
The data visualization space is crowded. There are lots of tools, each purporting to be the tool that solves your data woes and leads you to insight via illustrations. But while you may get good-looking graphs, you are probably not seeing the behind-the-scenes pain from IT: analytics dashboards and vertical applications take multiple meetings for gathering requirements, and they discover the direction wasn’t quite right the first time around.
SOAR with AT&T Cybersecurity and Dark Reading
Watch the full video on our site. If you prefer reading, here’s the full transcript Terry Sweeney - Contributing Editor, Dark Reading Sanjay Ramnath - Associate Vice President, Product Marketing, AT&T Cybersecurity Terry Sweeney: Welcome back to the Dark Reading News Desk. We’re here at the RSA Conference in San Francisco.
Countdown to CCPA: 5 Questions You Need to Ask
The California Consumer Privacy Act of 2018, known as CCPA, is a data privacy law aimed at protecting the personal information of California consumers. Frequently compared to the UK’s expansive GDPR, CCPA will have a big impact on how companies collect, store, and process personal information of California consumers.
Notable Ransomware Attacks from 2019 and Lessons Learned
“We have your precious data! Pay us or lose it forever!” This is a message no organization or individual ever wants to see. Nevertheless, given trends over time in cyber security, ransomware remains a concern for many organizations. Here is a look at interesting examples of successful ransomware attacks and some lessons we can learn from each.
Practical security recommendations - for you and your business
Cybercrime is costing UK businesses billions each and every year. Small businesses in particular are under threat, as they often take a more relaxed approach and a ‘not much to steal’ mindset. However, this lack of diligence has caused many companies to close permanently. Let’s ensure yours isn’t one of them. Time to start making the issue a priority! Here are some practical security recommendations for you and your business.