Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
How to Ensure Physical Security of Your Company's IT Infrastructure?
Physical security includes measures and precautions designed to guarantee the physical protection of IT assets such as facilities, equipment and other properties from damage and unauthorized physical access. Physical security aims to protect such assets from physical threats like theft, manmade catastrophes, accidental damage, fire and other natural disasters. It is an essential part of a security plan and is an indispensable component of all security efforts.
Is Cultural Transformation the Secret to Productivity?
If you suspect that your employees are wasting time on the job and they are not performing up to expectations, it might be time to transform the culture of your organization. A company with a toxic culture runs the risk that employees will remain disengaged and productivity will decline even further. As a leader, you have the perfect opportunity to make improvements by building a culture of support and respect and strengthening teamwork.
Vulnerability Scanning Services: 2-minute overview
A Guide to Mobile TLS Certificate Pinning (2019)
Cybersecurity professionals know what they’re up against. The type, number and severity of cyberattacks grows with time. Hackers display no shortage of cunning and ingenuity in exploiting security vulnerabilities, compromising important data and inflicting damage to both individuals and organizations. Cybersecurity professionals also know that their defenses must evolve along with the attacks, requiring them to display even more ingenuity than hackers when creating security tools.
Is cyber security magic, or just an illusion?
Magic seems to be very popular at the moment. Just look at last week’s Britain’s Got Talent, which featured an improbable number of magicians in its line-up. These included ‘X’, the masked magician who was wearing something that looked suspiciously like an anonymous mask and managed to supposedly hack Instagram. A lot of cyber security technology seems to work like magic, so is this a coincidence? Is ‘X’ a reformed hacker turned stage magician? Spoiler alert: no.
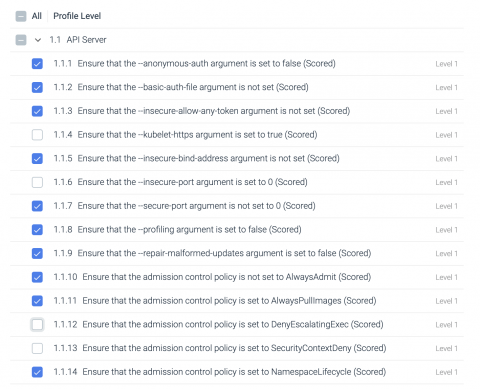
Custom compliance filters with Sysdig Secure
Custom compliance filters is now GA as part of the SaaS and on-prem release. With Sysdig Secure, enterprises can enforce compliance filters across the container lifecycle. Teams can automate regulatory compliance controls for PCI, NIST, CIS, for Kubernetes and container environments at scale.They also gain visibility into the performance, health, compliance, and security posture of an on-prem and/or multi-cloud environment from a single dashboard.
Weekly Cyber Security News 07/06/2019
A selection of this week’s more interesting vulnerability disclosures and cyber security news. A great (or bad depending on how you look at it) example of a supply chain infection this week, luckily it was spotted and a pre-emptive move taken to divert funds before they were stolen. They were very lucky in this case.
How to Advance ICS Cybersecurity: Implement Continuous Monitoring
Industrial Control Systems (ICS) include Supervisory Control and Data Acquisition (SCADA) systems, Distributed Control Systems (DCS) and other control system configurations such as Programmable Logic Controllers (PLC). They are typically used in industries such as electric, water, oil and natural gas, transportation, chemical, pharmaceutical and manufacturing (e.g., automotive, aerospace). These control systems are vital to the operation of U.S.
What is Database Security?
Database security refers to the various measures organizations take to ensure their databases are protected from internal and external threats. Database security includes protecting the database itself, the data it contains, its database management system, and the various applications that access it. Organizations must secure databases from deliberate attacks such as cyber security threats, as well as the misuse of data and databases from those who can access them.
Swimming in the Deep End: Data Leaks and the Deep Web
Those interested in how data breaches occur should be familiar with the general topography of the Internet. In our previous piece, we discussed the difference between the surface web, deep web and dark web. Most estimates about the topography of the Internet conclude that the deep web makes up between 95%-99% of all web sites. The dark web likely comprises less than 1%, while the surface web accounts for only a few percentage points itself. Nearly the entire Internet is the deep web.