Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Monitoring Logs for Insider Threats During Turbulent Times
For logs and tracking insider threats, you need to start with the relevant data. In these turbulent times, IT teams leverage centralized log management solutions for making decisions. As the challenges change, the way you’re monitoring logs for insider threats needs to change too. Furloughs, workforce reductions, and business practice changes as part of the COVID stay-at-home mandates impacted IT teams.
Unraveling open port threats and enhancing security with port scanning tools
From exposing your network vulnerabilities to becoming a passageway for intruders, open ports can pose several risk vectors that threaten your network’s confidentiality, integrity, and availability. This is why it’s a best practice to close your open ports. To tackle the risks introduced by open ports, network admins rely on port scanning tools to identify, inspect, analyze, and close open ports in their networks.
Cybersecurity and accessibility for Ecommerce platforms: Is it possible?
Ecommerce store losses to online payment fraud are expected to reach $25 billion by 2024, a new Juniper report reveals — up from just $17 billion in 2020. Undoubtedly, cybersecurity should be a top priority for ecommerce owners. At the same time, accessibility is another pressing concern, with the need for websites to comply with the World Wide Web Consortium's Web Content Accessibility Guidelines (WCAG 2.0 AA).
Detectify Security Updates for March 23
Our Crowdsource ethical hacker community has been busy sending us security updates, including 0-day research. For Asset Monitoring, we now push out tests more frequently at record speed within 25 minutes from hacker to scanner. Due to confidentially agreements, we cannot publicize all security update releases here but they are immediately added to our scanner and available to all users. The following are some of the security vulnerabilities reported by Detectify Crowdsource ethical hackers.
CloudCasa Demo - Persistent Volume Backup Utilizing on Amazon EKS Cluster
Data Protection for SUSE Rancher Managed Clusters is Easy with CloudCasa
Why you Need Data Protection for Kubernetes Now that you have SUSE Rancher managing your Kubernetes applications, you need to consider how to further protect your application data. While Kubernetes is designed to provide a zero-downtime environment, service interruptions can happen, as well as human and programmatic errors and of course the dreaded ransomware and cyber-attacks.
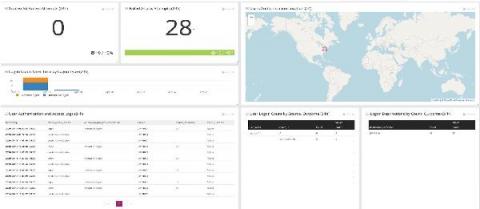
Where do You Stand on the Top Threat Intelligence Considerations?
We conducted a community survey in January and invited visitors to our website to answer four questions.
AWS S3 security with CloudTrail and Falco
One of the major concerns when moving to the cloud is how to approach AWS S3 security. Companies may have moved their workflows to Amazon, but are still cautious about moving their data warehouse. And that is totally understandable. We have all heard about data breaches in companies like Facebook, GoDaddy, and Pocket. It’s important that access to information is done properly, in a limited and controlled fashion, to avoid such breaches.
Employee Well-Being Is Every CEO's Responsibility
As we address a number of anniversaries related to the COVID-19 pandemic, you’re likely reminded of a lot of the uncertainty you were feeling coming into an indefinite work from home scenario. I know I certainly am.
We're All WFH Too - One Year Later!
Last year brought a lot of change. Companies across the globe had to pivot, ready or not, and many went fully remote just like we did here at Veracode.