Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
OWASP Top 10 API security vulnerabilities | API security risks
5 Ways Your Cryptocurrency May be Hacked
Over time technologies evolved and now things that seemed to be not possible several years ago become the reality. Now you can order food, services, and basically anything you need online, and pay for it without leaving home. No surprise here, that cash payments are becoming a relic of the past. Along with wireless payments like Google or Apple pay (that still require assigning a banking account or card i.e. physical currency), the cryptocurrencies like Bitcoin are getting widely used.
Unveil hidden malicious processes with Falco in cloud-native environments
Detecting malicious processes is already complicated in cloud-native environments, as without the proper tools they are black boxes. It becomes even more complicated if those malicious processes are hidden. A malware using open source tools to evade detection has been reported. The open source project used by the malware is libprocesshider, a tool created by Sysdig’s former chief architect Gianluca.
Bits of Security, Snyk.io: Stranger Danger: Finding Security Vulnerabilities Before They Find You!
Bits of Security, PedidosYa: Fraud Detection using Datadog and Sherlock
Taking an IT-Focused Approach to Securing OT Remote Operations at Municipal Utilities May be Risking Lives
The Oldsmar, Florida, water breach is two months behind us, but the lessons learned will continue to reverberate for thousands of budget-constrained municipal utilities in North America, as well as other regions across the world.
Cloud Threats Memo: LinkedIn Spearphishing and Malware-as-a-Service
‘More_eggs’ is a backdoor sold as a “malware-as-a-service” (MaaS) by a threat group known as “Golden Chickens” and predominantly used by three criminal groups: FIN6, Cobalt Group, and Evilnum. In the latest campaign, unearthed by researchers from eSentire and targeting a professional working in the healthcare technology industry, a threat actor is exploiting fake job offers on LinkedIn to deploy the ‘More_eggs’ backdoor on the victim’s machine.
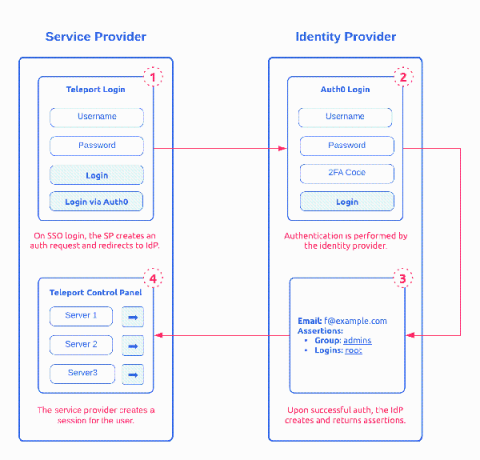
How SAML 2.0 Authentication Works?
Security Assertion Markup Language (SAML) 2.0 is one of the most widely used open standard for authentication and authorizing between multiple parties. It’s one of the protocol that give users the single sign-on (SSO) experience for applications. The other adopted open standard is OAuth and OpenID. Of the two, SAML 2.0, released in 2005, remains the 800 pound gorilla in Enterprise SSO space. This post provides a detailed introduction on how SAML works.
Domain Controller: LDAP Server Signing Requirements
The Biggest Breaches and Data Leaks of 2020
Year after year, cyberattackers cause unnecessary stress for organizations, disrupting innovation and impacting profit. 2020 was no different – last year brought a bevy of damaging breaches that cost organizations precious money and time they couldn’t get back. Ranging from thousands to billions of records exposed, breaches big and small gave threat actors access to sensitive information like email addresses, locations, passwords, dates of birth, and more.