Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Training, Accountability and Assessment: Three Priorities for Raising Privacy Awareness Within Your Team
Employees, contractors, and vendors have unparalleled access to company data, requiring careful adherence to data privacy best practices to secure personal information. Unfortunately, many employees are either unaware of these practices or are unwilling (or forgetful) to regularly implement them into their workflows.
4 ways Security and DevOps can collaborate to reduce application vulnerabilities
Digital transformation moves application security to the top of mind list!
Here are some insights from AVP, Cybersecurity Todd Waskelis as we discussed cybersecurity and application security in focus.
Introducing AT&T's Managed Endpoint Security with SentinelOne
With 5G, edge solutions, and digital transformation all around us, every enterprise should be taking a closer look at their endpoint security and evaluate options that will be able to keep pace with this dynamic new environment.The newly introduced AT&T Managed Endpoint Security with SentinelOne™ offer brings world class managed services with comprehensive endpoint security.
Red teaming vs pentesting - What is the difference and impact on your cyber security strategy
Learn about:
+ What is Red Teaming?
+ Business Benefits of Red Teaming
+ Red Teaming Methodology
+ Common Terms & Acronyms
+ What is Penetration Testing?
+ Business Benefits of Penetration Testing
+ Pentesting Methodology
+ When should you consider a red team assessment?
+ When you are asking for a ‘red team’ and don’t need one.
+ When you are asking for a ‘pen test’ and don’t need one.
Code Dx 5.3 integrates with Snyk for comprehensive vulnerability management
The Code Dx team is pleased to announce the general availability (GA) of Code Dx 5.3, which notably features an integration with Snyk to help customers integrate open source and container security into their continuous development processes. As we move toward a cloud native world, we’re working to ensure that developer-first tooling, secure cloud infrastructure, container security, and open source tools are fully integrated into Code Dx 5.3.
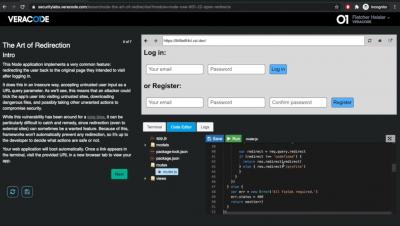
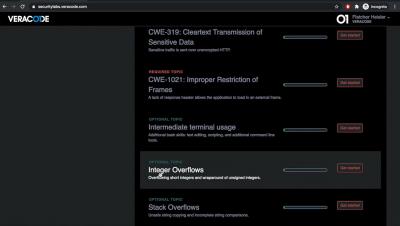
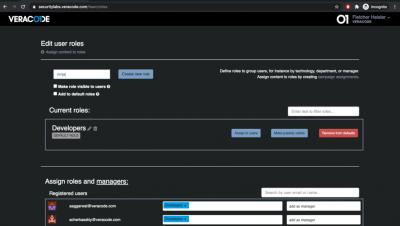
OWASP Top 10: Insecure Deserialization Security Vulnerability Practical Overview
Insecure Deserialization is #8 in the current OWASP Top Ten Most Critical Web Application Security Risks. It is difficult to exploit, but successful attacks can lead to remote code execution.