Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
The factors that determine the cost of cyber insurance
In our predictions, we highlight how cybersecurity will become a key area for insurers in 2022. The seriousness and growth in damages caused by cyberthreats has raised the price of policies sharply in 2021, according to experts. Given this situation, companies must either be prepared to take out new insurance at higher rates or expect a rise in the cost of their current policy. But what elements determine the cost of cyber insurance for insurers? There are 5 key factors, both internal and external.
CVE-2021-44521 - Exploiting Apache Cassandra User-Defined Functions for Remote Code Execution
JFrog’s Security Research team recently disclosed an RCE (remote code execution) issue in Apache Cassandra, which has been assigned to CVE-2021-44521 (CVSS 8.4). This Apache security vulnerability is easy to exploit and has the potential to wreak havoc on systems, but luckily only manifests in non-default configurations of Cassandra.
What it's like to be Head of People at Tines: An interview with Maria Dillon
As Head of People at Tines, Maria Dillon champions our inclusive company culture. Maria supports every team as we rapidly scale, ensuring every voice is heard and implementing thoughtful initiatives that help set Tines apart as a world-class employer and a fantastic place to work.
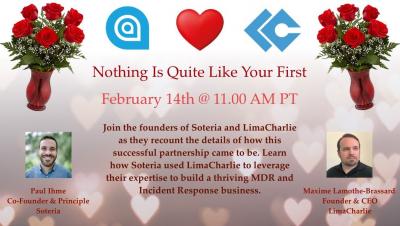
A Cybersecurity Love Story
Optimized Traffic Mirroring Examples - Part 2
In a previous post, we looked at an example of a fictional bookstore company and recommended mirroring strategies for that specific scenario. In this post, we’ll be looking at a fictional bank and recommended mirroring strategies for their network traffic. For a list of the most commonly used strategies, check out our traffic mirroring tutorial.
SOX Audit Compliance Requirements For 2022
ManageEngine is recognized as a December 2021 Gartner Peer Insights Customers' Choice for Privileged Access Management
ManageEngine’s privileged access management (PAM) suite of products have helped over one million IT administrators and users around the globe efficiently manage their privileged credentials and access. On that note, we’re excited to announce that we’ve been recognized as a Gartner Peer Insights Customers’ Choice for Privileged Access Management!
Wire Technologies Appoints Nuvias as Sole Distributor in the UK
XDR: Native vs. Open explained
With the advent of extended detection and response (XDR), the security analyst’s need for one complete, contextualized view into threats across the enterprise is becoming less fantasy and more reality. XDR promises a faster and more efficient way to bring together data from a range of security tools, spot sophisticated attacks, and automate response actions to protect a growing number of assets within the traditional network perimeter and beyond.