Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Unified Security for a Reconnecting World
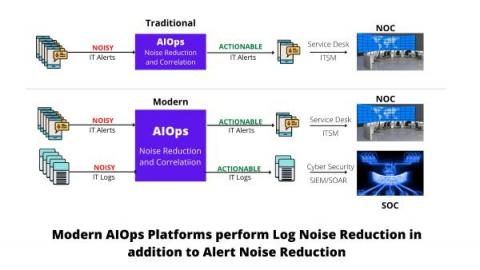
Can your AIOps platform do Log Noise Reduction in addition to Alert Noise Reduction? If not, it is time to re-evaluate your AIOps
8 Must-Ask Questions to Consider: Rubrik Ransomware Recovery Assessment
2021 was the year of ransomware. You couldn’t watch or read the news without hearing about another business falling victim. Cybersecurity Ventures estimates that a ransomware attack took place every 11 seconds in 2021, with global damages reaching an estimated $20 billion – that is 57x more than it was in 2015. Unfortunately, the reality is that ransomware is here to stay, and every organization, regardless of industry or size, is a potential target.
Recent Examples of Zero Day Attacks & How to Avoid Them
Zero day attacks consist of almost 80% of all malware attacks. Take a look at some recent attacks and learn how to prevent them. You work hard to secure your business network. Yet determined hackers probe persistently until they find a software vulnerability you don’t know about. They use this previously unknown and unpatched flaw.
DDoS Protection With AppTrana
Ep 5 Securing the digital supply chain - Sai Kalur
1Password: The Heart of Cybersecurity Webinar Series: Jessica Barker
7 Best Practices for Effective Third-Party Cyber Risk Management
While the digital world provides many benefits, there are also various risks involved within the third-party risk category. Also, the category of the risks can be quite long i.e. financial, environmental, security risk and reputational. Firms are often required to open their network and share data related to the company, employees, customers etc. which puts them at significant risk of cybersecurity issues, breaches and loss of sensitive data.
Hackers Disrupt Port Operations in Europe
Weekly round-up of the most noteworthy cyber security headlines.
Secure yourself with our digital declutter checklist
A digital declutter helps you organize your life and has the added bonus of reducing your vulnerability to common threats. But knowing where to begin can be hard – most of us leave a larger digital footprint than we realize. We’ve created a checklist to help you clear away the clutter and reap the rewards of a clean digital state.