Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
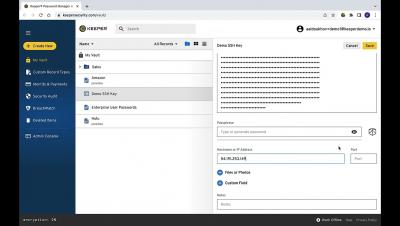
Keeper Commander - Using SSH Command
Keeper Commander can establish basic SSH connections through the command line interface on any device using the native SSH connection tool. Commander's ssh command provides instant SSH connections for any "SSH" Record Type in the vault. To create an “SSH” type record in your vault, create a new record and select “SSH key” as your record type. Paste your private key to the appropriate field in your record and populate the login and hostname fields.
Cyberpion Closes Series A Funding at the Inflection Point for Attack Surface Management
In business and life, getting the timing and the team right is half the battle.
Improve Your Web Applications and Your Client-side Security
Learn how to protect your client-side web applications and the customer data you collect via your websites. Gain a deep understanding of how to stop skimming breaches by closing gaps in your web application firewalls, content security policies, penetration testing, security testing, and vulnerability scanning coverage. Explore the basics of client-side security and learn how businesses can protect themselves and their customers with automated tools, monitoring, and controls to stop threats, all while safeguarding customer data.
The Ultimate Guide to Client-Side Security Executive Summary
In a world in which commerce, business, and information are driven almost exclusively by the internet, protecting both consumers and data is critical.
Tines: How Auth0's engineering team tamed incident response with no-code automation
No-code automation isn't just for non-technical users. Programmers have enough code to maintain as it is, so when they want to build an important workflow to improve how the team works, it's great to be able to skip all the baggage like logging, monitoring, persistence, backups, and deployments. Join Tines and special guest Dennis Henry, Sr. Engineering Manager at Auth0, as we dive into one such real use case - engineering incident response. When engineers are focused on triaging an issue, the last thing they should be worrying about is the tooling they are using to organize their response.
Tigera: Microsoft and Tigera: Hands-on AKS workshop - Implementing Zero-Trust Security for Containers
In this AKS-focused workshop, you will work with a Calico and Microsoft expert to learn how to implement Zero-Trust security for workloads running on AKS. This 90-minute hands-on lab comes with your own Calico Cloud environment. Join us to learn how to: We have limited the number of participants for this workshop to ensure that each participant can receive adequate attention. Register now to reserve your spot!
Tigera: Best practices for zero-trust workload security on EKS clusters
Cloud security teams are focussing on building and maintaining a zero-trust model to secure access to their critical data and protect workloads from malware. As most enterprises operate in a hybrid or multi-cloud model, controlling egress traffic for workloads is a key step towards building a zero-trust environment. Calico and EKS work in unison to simplify zero-trust workload security on AWS EKS clusters.
Tigera: AWS Dev Days: Hands-on EKS workshop: Configuration Security and Compliance
In this EKS-focused workshop, you will work with AWS and Calico experts to learn how to design and deploy best practices to secure your Kubernetes environment and achieve compliance with regulatory frameworks including but not limited to PCI, SOC2 and GDPR. This 90-minute hands-on lab comes with your own provisioned EKS and Calico Cloud environment and is designed to help implement.
World Backup Day: Simplicity and Patience is Key
A few months ago, a popular cybersecurity news organization posted an urgent notice on social media seeking help to recover their data after their blog was deleted. They announced that they had no backups and they were desperately trying to contact the site administrator to restore their blog collection. This was as maddening as it was embarrassing for the same reasons.