Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
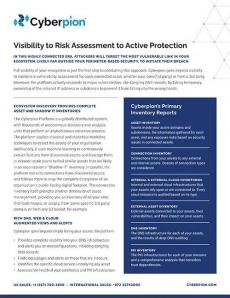
Visibility to Risk Assessment to Active Protection
Tigera: AWS Dev Days: Hands-on workshop: Implementing container security on EKS
WatchGuard: The Critical Factors to Look for in a Cybersecurity Vendor
The Top Benefits Of XDR
Attention business owners: Top 5 Cybersecurity questions to ask in 2022
Wayne Bridgeman II, a Senior Manager on AT&T’s Network Cybersecurity team, offers a 5-point checklist for businesses in 2022 alongside tidbits of often overlooked tactics that can strengthen security.
Lookout and HPE Aruba Announce Integrated SASE Architecture
To streamline networking management and modernize IT operations organizations are deploying software-defined wide area network (SD-WAN) systems. But as networking becomes cloud-delivered, security often lags behind. With data and applications moving to the cloud, you need an efficient way to secure the activities that are going on between branch locations and the cloud.
New OpenSSL critical vulnerability: What you need to know
On Oct 25, 2022 The OpenSSL project announced a forthcoming release of OpenSSL (version 3.0.7) to address a critical security vulnerability. This release should go live on Tuesday, November 1, 2022 between 1300 and 1700 UTC. Snyk has published a placeholder advisory with the current known details, and will update the advisory when official vulnerability details are publicized. The last critical vulnerability in OpenSSL was released in 2016.
Code Signing Certificate - SSL2BUY Review by Jordy
Trustwave Launches Value-Driven Enterprise Pen Testing Offering
Trustwave has enhanced its pen testing offering to now include a high-quality, cost-effective offering to larger organizations. This new Enterprise Pen Testing (EPT) offering is designed to meet the complex testing needs of these organizations with an extensive breadth and depth of vulnerability identification, ability to deliver scaled programs of work, at an extremely competitive price point.
Why Identity Verification Is Important for Onboarding in a Remote Working Environment
Working and collaborating remotely is easier than ever in today’s digital age. As a result, the number of vendors engaging with businesses to execute job assignments has increased dramatically. People working remotely as independent contractors range from software engineers to copywriters. Because these folks will not be going into the office, Identity Verification is now an essential element of the Vendor Onboarding process. Why?