Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
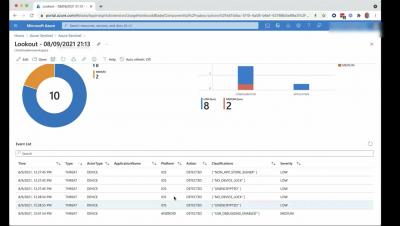
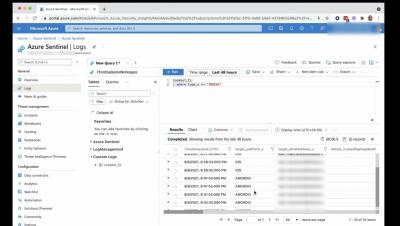
Lookout + Microsoft Azure Sentinel - Query Lookout threat intel from within Microsoft Azure Sentinel
Could your kids spot this mobile phish?
I realized early on that if I didn’t teach my kids how to identify and avoid likely attacks on their laptops and phones, that no one would. Nevertheless, when I see an opportunity for a “teachable security moment” I grab it, and last week this mobile phishes appeared on my phone. I captured a screen shot to share with my children and we played a little “spot the phish” game, where they would point out all the things that made this text suspicious.
Popular JavaScript Library ua-parser-js Compromised via Account Takeover
A few hours ago, an npm package with more than 7 million weekly downloads was compromised. It appears an ATO (account takeover) occurred in which the author’s account was hijacked either due to a password leakage or a brute force attempt (GitHub discussion).
Securing Google Cloud Platform with Sysdig
Forward Networks Wins "Enterprise Cloud Computing Software of the Year" Award in 2021 Mobile Breakthrough Awards Program
DBatLoader: Abusing Discord to Deliver Warzone RAT
67% of the malware downloads Netskope blocks come from popular cloud applications being abused by attackers. One of the services commonly abused by threat actors is Discord, which is abused to host malware such as TroubleGrabber using public attachment URLs. In this blog post, we will analyze a recent DBatLoader (a.k.a. ModiLoader) sample that uses this technique on Discord to deliver a malware known as Warzone (a.k.a. Ave Maria), a Remote Access Trojan created in 2018.
Internxt
5 Tips for the CISO Looking to Get a Handle on Cloud Security
Over the last 18 months, cloud application use has skyrocketed, with the average organisation with 500-2,000 employees now using 805 different cloud applications. This is a staggering level of new risk for CISOs to get their heads around. At the same time that cloud use has grown, so too have the efforts of malicious actors to target cloud applications which are all too often poorly secured and present a constant opportunity of unsecured data to compromise.