Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Secure your infrastructure from code to cloud
Leveraging Artificial Intelligence for Impactful Cybersecurity
Artificial intelligence (AI) is reinventing the trajectory of cybersecurity and fighting with a double-edged sword. If harnessed correctly, AI can automatically generate alerts for emerging threats, detect new types of malware, and protect sensitive data. While it has advanced us into a plethora of new technologies -- think Siri, facial recognition, and Google’s search engine -- it has also probed us with significant threats from cybercriminals.
Egnyte Releases Open Source Bandwidth Limiting Plugin
Bandwidth pricing is a major component of the cloud services model. And for a content-heavy service like a video or document store, egress costs can quickly spiral out of control. To mitigate this, it is important to put limits on the amount of data that can be downloaded in a given interval. However, bandwidth limiting for a multi-tenant SaaS product adds a few interesting challenges.
Our Answers to the 7 Questions SRM Leaders Should Ask OT Security Providers
CrowdStrike 2021 Cloud Workload Protection Platform (CWPP) Buyers Guide
Sharpen your security skills with open source! Introduction to modern infrastructure access
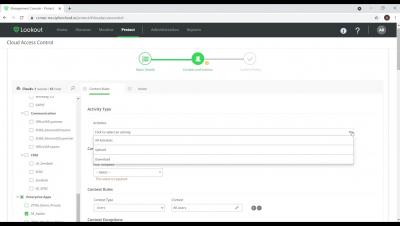
Lookout CASB Protects your Business
Lookout ZTNA - Creating Policies for data protection and application security
Accelerating the Snyk infrastructure as code vision with the addition of CloudSkiff
We are thrilled to welcome the team at CloudSkiff to Snyk! Many of you may be more familiar with driftctl, the open source project started by the CloudSkiff team. I wanted to share with you why we’re excited about the addition of this fantastic group of people to Snyk, and our plans for the future of Snyk Infrastructure as Code (Snyk IaC), as well as our commitment to keeping driftctl open source.