Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
The rising trend of malicious packages in open source ecosystems
Since the beginning of 2023, Snyk has documented around 6800 malicious packages across PyPI and the npm registry, which requires little to no interaction, almost 860 of which were discovered by us.
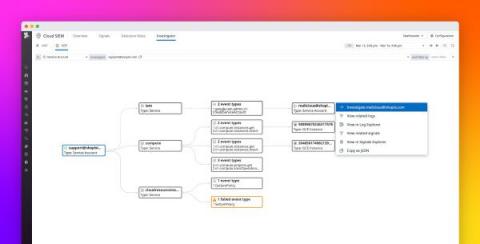
Visualize activity in your Google Cloud environment with Datadog Cloud SIEM Investigator
Cloud environments, in all their dynamic complexity, demand careful monitoring by DevOps and security teams. But the sheer abundance of telemetry data associated with the thousands of resources, users, and roles that comprise these environments can make monitoring a formidable task, causing security risks and other issues to be all too easily overlooked.
Emerging Chatbot Security Concerns
In late 2022, artificial intelligence (AI) chat and conversational bots garnered large followings and user bases. AI chatbots, including ChatGPT, Meta’s Blender Bot3 and DeepMind, and Google’s Sparrow, have numerous benefits and uses, including potentially replacing current search engines, but there are notable drawbacks.
The Shift to the Cloud and its Implications for Application Security
Everybody’s doing it: shifting applications to the cloud. More flexibility. More storage. More scalability. But how does this affect application security? What challenges does it present?
CrowdStrike's Artificial Intelligence Tooling Uses Similarity Search to Analyze Script-Based Malware Attack Techniques
According to the AV-TEST Institute, more than 1 billion strains of malware have been created, and more than 500,00 new pieces of malware are detected every day. One of the main reasons for this rapid growth is that malware creators frequently reuse source code. They modify existing malware to meet the specific objectives of an attack campaign or to avoid signature-based detection.
Coffee Talk with SURGe: Oakland Ransomware Attack, BreachForums, Acropalypse Vulnerability, GPT-4
How to Handle AWS Secrets
In this blog post, we'll cover some best practices for managing AWS secrets when using the AWS SDK in Python.
Ultimate Security Checklist to Launch a Mobile App in the United Kingdom - iOS & Android
Mobile apps have made our lives a lot easier. From ordering food, watching movies, booking a cab, and sending money, one can do everything via mobile apps. However, while mobile apps are a great utility, they've become an easy target for scammers, hackers, and cyber attackers, especially in countries like the UK. Taking charge of the situation, the UK government has created strict guidelines for enhancing the security of mobile apps.
Top 6 Cloud Insider Threats You Need To Be Aware Of
Cloud computing is the most cost-effective way to store and manage data and meet growing business demands today. However, the rapid rise of cloud usage means you need to stay alert to potential cloud security insider threats that can compromise your sensitive data and security posture. In this post, we discuss the insider threat landscape, explore several types of cloud insider threats, and examine the best practices to combat these threats.