Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Not a SIMulation: CrowdStrike Investigations Reveal Intrusion Campaign Targeting Telco and BPO Companies
CrowdStrike Services reviews a recent, extremely persistent intrusion campaign targeting telecommunications and business process outsourcing (BPO) companies and outlines how organizations can defend and secure their environments.
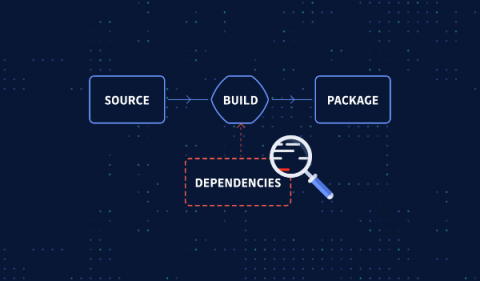
9 Things to Consider When Choosing an SCA Tool
Software composition analysis is an essential part of application security. Here are the important factors to consider when selecting an SCA scanner to be sure it is well-suited to your needs.
[Webinar] Taming Secrets Sprawl with Doppler and GitGuardian
File-level Backup vs Image-level Backup
Security Awareness Training for Employees - Tips to Protect Your Staff At Co-Working Spaces
Westcon-Comstor reinforces its commitment to driving sustainability in the channel with new ESG lead for EMEA
The troubles of being on Cloud9: Why your browsers are not safe
With the new browser botnet, Cloud9, waiting to penetrate your browsers remotely to access and steal your sensitive and confidential data, it can be challenging to stay safe while browsing the internet. As reported by Bleeping Computer, this Remote Access Trojan named Cloud9 allows cyberattackers to execute commands remotely to steal your data. This malicious extension is not found in the Chrome store, but has been reported to be installed by other means. What’s the story of Cloud9?
Interview With Founder Jacob Hess
For the next interview in our series speaking to technical leaders from around the world, we’ve welcomed Jacob Hess, Founder at NGT Academy. Jacob Hess is the co-founder of NGT Academy, an immersive, military-grade cybersecurity and IT professional training platform founded by former military technicians from the US Air Force that has equipped thousands of military engineers with top security clearances.