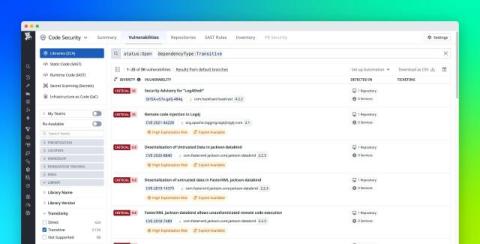
Remediate transitive vulnerabilities faster with Datadog Software Composition Analysis
Security teams are responsible for finding and remediating vulnerable dependencies within applications that are built from large ecosystems of frameworks, SDKs, and utilities. What makes this task especially challenging is that these dependencies can pull in dozens or even hundreds of transitive dependencies through complex dependency chains. Even when scanners identify what’s vulnerable, teams still often lack the information they need about the dependency chain to safely address the issue.