Securing Remote Access: Best Practices for Third-Party Risk Management
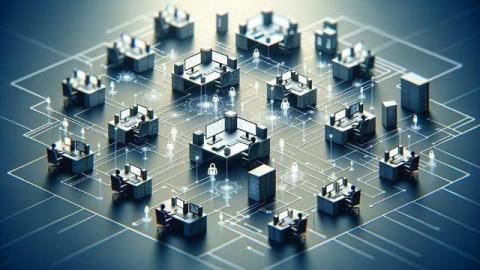
The physical location of users has become less and less important in conducting business, with the drawback that it creates new, persistent threats to organizations. You know that. You may not know that remote access to IT and business-critical systems is not a new concept. It’s been around since the late 1980s.