How to Install and Configure Infosec Multicloud
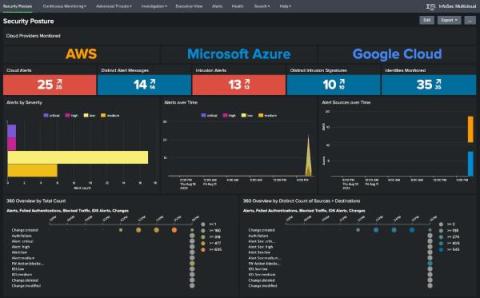
The Infosec App for Splunk is your starter security pack. It's designed to address the most common security use cases, including continuous monitoring and security investigations. The new Infosec Multicloud App for Splunk is designed by our field team to help customers that have a cloud environment. In addition to views of security posture across cloud providers, the app includes a billing dashboard for a high level overview of costs spread across your various cloud providers.