Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Getting Value from Your Proxy Logs with CrowdStrike Falcon LogScale
What's SIEM? Security Information & Event Management Explained
How to Get a Job in Cybersecurity by Leveraging LinkedIn
Landing a SOC job and breaking into the cybersecurity space can feel daunting. One way to set yourself up for success is to leverage professional social networking sites like LinkedIn. When used correctly, LinkedIn can be a powerful tool for growing your connections and landing your dream gig. Not sure how to get a job in cybersecurity by using LinkedIn? Here are some tips.
Coffee Talk with SURGe: 2023-OCT-17 Cisco IOS XE, Signal Zero-Day Rumor, Conflict Disinformation
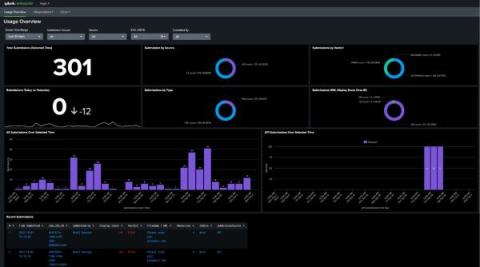
Introducing Splunk Add-On for Splunk Attack Analyzer and Splunk App for Splunk Attack Analyzer
Cybersecurity: An Introduction & Beginner's Guide
How to Build Your Cybersecurity Leadership Skills as a SOC Analyst
Leadership skills are important for career growth in any industry, and cybersecurity is no exception. While you can certainly have a long, fulfilling career as a SOC analyst, you may be interested in moving up the ranks into a leadership position one day. Whether you aspire to be a SOC director or even a CISO, these tips will help you position yourself and develop the skills needed to move into a cybersecurity leadership role.
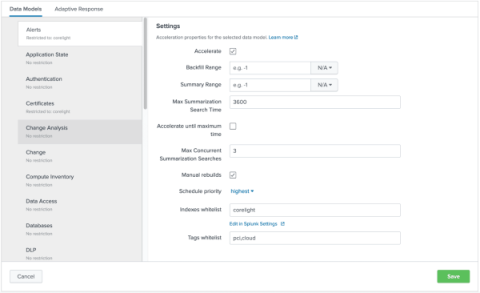
Enhance your search experience within Splunk by using the Corelight App
The Corelight App for Splunk provides the foundation for organizations to boost SOC effectiveness and productivity by using Corelight data in Splunk. In this blog, I’ll walk through how the Corelight App leverages Splunk’s Common Information Model (CIM) to enhance users' search experience when they are using Corelight data.