Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Coronavirus: 10 Steps Employers Should Take to Maintain a Safe Workplace
As we’re actively in the throes of COVID-19, it’s understandable that workers and employees are uneasy about their safety and security on the job. Here are 10 steps employers need to take to keep your workplace safe in the face of a public health emergency.
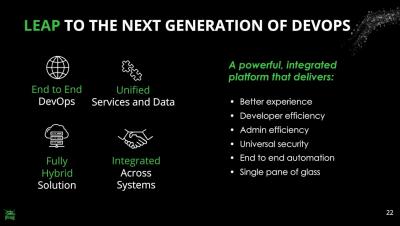
DevSecOps Best Practices with JFrog Platform
Application Security Testing Trends
According to a recent Forrester report, the application security market will exceed $7 billion by 2023, with security scanning tools leading. Clearly, organizations increasingly understand that securing their application layer is important, and they are prepared to invest substantial resources in protecting it.
CyberGRX vs UpGuard Comparison
Robust vendor risk management practices has never been more important. It is increasingly one of the top concerns of CISOs around the world. This is because outsourcing, digitization, and globalization have changed the way we do business over the last few decades. These forces have led to innovation in products and services, the ability to focus on core competencies, reduced costs, and new global markets.
The Future is Hybrid: Practicing Security in the Hybrid Cloud
By now, many organizations have adopted the cloud in some way. We saw organizations moving whole servers over to the cloud at the beginning, but now we see small parts of a system being moved to the cloud and new cloud native offerings. We’ll use the analogies of Lincoln Logs and Legos to describe these deployment models.
Third-party data breach exposes GE employees' personal information
Past and present employees of General Electric (GE) are learning that their sensitive information has been exposed by a data breach at a third-party service provider. Fortune 500 company GE says it was recently informed of a security breach at one of its partners, Canon Business Process Services.
Elastic SIEM is free and open for security analysts everywhere
Security teams must protect attack surfaces that are becoming bigger and more distributed due to the growth of remote work, cloud infrastructure, and other dynamics. These teams understand that meeting this challenge at scale requires the successful incorporation of the appropriate technology into their security operations program.
Coronavirus Impact on Cyber Security
The Coronavirus (COVID-19) pandemic is increasing tremendously and disrupting the global health at large extent, in addition to the damages to economics, social and political systems. More importantly, the digital world is also on the verge of destruction because, due to this menace, the people at large scale are compelled to work remotely and doing so will make them rely heavily on remote communication and digital tools.
Should you be worried about false negative insider threats?
The consistent rise in Insider Threat-related incidents has led to a growing focus and investment in proactively detecting these threats. According to reports, 60% of organizations discovered one or more insider attacks last year, and 90% admitted that they felt vulnerable to insider attacks. Reports also show that it takes an average of over two months to contain an insider attack.