Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Fixing Shadow APIs: Why True Remediation is Critical in the Age of AI
Fixing Shadow APIs: Why True Remediation is Critical in the Age of AI Agentic AI is fundamentally changing the security landscape, transforming how we think about API protection. In this insightful discussion, A10 Networks security experts Jamison Utter and Carlo Alpuerto dive deep into the challenges presented by this new wave of automation and API consumers.
Vibe Code Prompt to Build an Application!
Vibe Code Prompt to Build an Application!
How Arctic Wolf Delivers Managed Detection and Response with Broad Visibility and Proactive Security
In this Managed Detection and Response overview, we see how Arctic Wolf delivers 24x7 monitoring, broad visibility, response capabilities and proactive security recommendations to our customers leveraging their existing security tools and the Aurora Platform.
Tanium Converge 2025 Recap - Tanium Tech Talks
Tanium Converge 2025 announced some amazing tech! Join the Tanium talkers for an insiders look as we review what happened during this special week. Find out which keynotes to watch on-demand for free. Also check out the other in-person Converge interviews on the Tanium Tech Talks playlist on the channel here. Will we see you there in 2026? Tanium's 2025 Converge user conference was held November 17-20 in Orlando, Florida. Converge 2026 will be in Las Vegas, Nevada, November 16-19..
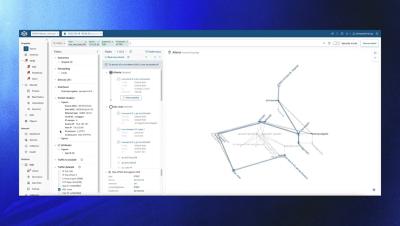
Introducing the New Security-Focused Path Search View in Forward Enterprise
Chris Naish from Forward Networks introduces a new security-centric feature in the Forward Enterprise release version 25.10. The Security Focused Path Search View highlights devices responsible for traffic restriction or IP address translation, improving network path comprehension for security analysis. This mode filters out non-restrictive hops, allowing security professionals to efficiently access crucial information.
Is AI taking entry-level jobs a good thing? #cybersecurity #ai #podcast
There's growing concern that AI automation is removing the hands-on experience junior analysts need to develop into senior defenders. In this Intel Chat, Matt Bromiley and Chris Luft challenge that assumption. Matt breaks down why the traditional entry-level path of endless log review and alert triage was never the best training ground to begin with. Log detection, alert triage, and drift detection are often cited as how defenders learn the trade. But most analysts never had time to get to drift detection because they were buried in repetitive work.
The Hacker Was Testing Shai-Hulud 2.0 Attack - 3 Days Before It Hit
We discovered hackers were testing Shai-Hulud 2.0 three days before the attack. Our researcher Guillaume Valadon explains how GitGuardian's data helped us warn hundreds of companies who didn't even know they were compromised.
Shai-Hulud 2.0: What did the hackers learn from the previous attack?
Watch our security researcher Guillaume Valadon break down the sophisticated ShaiHulud 2.0 attack where malware exfiltrates secrets directly to GitHub using stolen developer credentials.
Is PAM Really Solving Security Problems?
Privileged access management has long aimed to control powerful accounts, yet many environments still carry excessive permissions and weak accountability. Password vaults, rotating credentials and stronger governance place controls around admin accounts, linking PAM, access control and identity security to limit damage when something goes wrong.