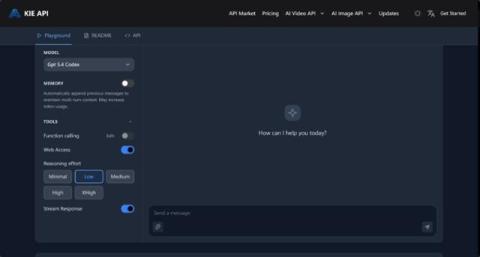
Codex API In DevSecOps: Balancing Developer Speed With Secure Code Review
AI-assisted coding is no longer a side experiment. It is becoming part of daily engineering workflows, from drafting functions and refactoring legacy code to generating tests and accelerating routine implementation work. That shift is why the Codex API now belongs in a broader DevSecOps conversation, not just a developer productivity discussion.