Cephalus Weaponizes Stolen RDP Credentials to Deploy Ransomware
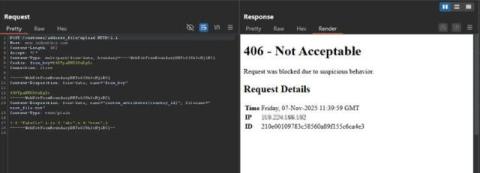
New research out of AhnLab documents the Cephalus ransomware group has been aggressively exploiting stolen Remote Desktop Protocol (RDP) credentials to break into networks and execute rapid, destructive encryption campaigns. The pattern is straightforward and brutal: credentials get you in, and once inside the attackers move fast to blind and break recovery.