Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Adding Container and IaC security to the Snyk plugin for Jetbrains
We’re excited to announce that infrastructure as code (IaC) and container security are joining code and open source dependency security in the free Snyk plugin for JetBrains IDEs. As of today, developers using JetBrains IDEs can secure their entire application with a click of a button. Snyk Security for JetBrains increases code security and reduces time spent on manual code reviews by empowering developers to find and fix issues within their JetBrains IDEs.
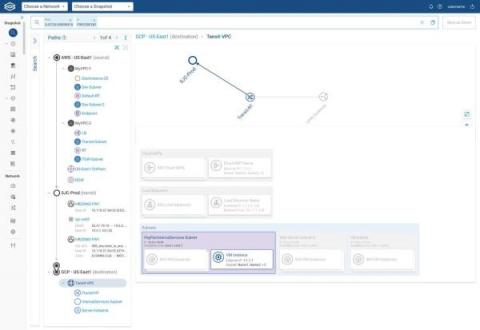
View All Your Clouds in a Single Pane of Glass
If your enterprise is like most of Forward Networks’ customers, then your IT shop oversees a sizable cloud estate. You probably have hundreds of accounts, projects, or subscriptions across different cloud vendors. There are tons of related objects too — virtual machines, firewalls, transit gateways, subnets, and more. And cloud-native apps? Maybe you hundreds of those in use or development as well.
Voice of the SOC Analyst report 2022
Security teams are being prevented from doing their best work. While understaffing and low budgets have always been challenges for any type of team, security teams are uniquely affected by repetitive, manual tasks, which in turn keep them from working on higher-impact projects that contribute to their organization’s overall security posture.
Developer Roll Up: February 2022
We are a couple of days late with the developer roll up for February but it is only because we are so busy! This is a huge update despite it being for the shortest month of the year, and we are not done yet: expect some even bigger announcements throughout March.
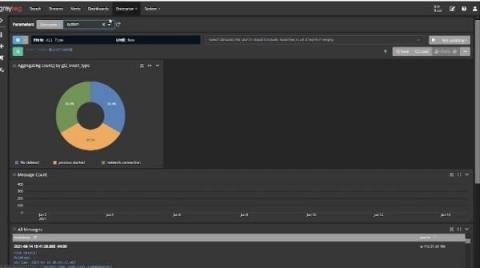
Using Log Management for Compliance
It’s that time of the year again. The annual and dreaded IT and security audit is ramping up. You just received the documentation list and need to pull everything together. You have too much real work to do, but you need to prove your compliance posture to this outsider. Using log management for compliance monitoring and documentation can make audits less stressful and time-consuming.
ITOps vs. SecOps vs. DevOps vs. DevSecOps
ITOps, SecOps, and DevOps may sound similar. Indeed, they are similar - to a degree. But they have different areas of focus, different histories, and different operational paradigms. Keep reading for an overview of what ITOps, SecOps, and DevOps mean and how they compare. We'll also explain where DevSecOps fits into the conversation - and why you shouldn't worry so much about defining these terms perfectly as you should about finding ways to operationalize collaboration between your various teams.
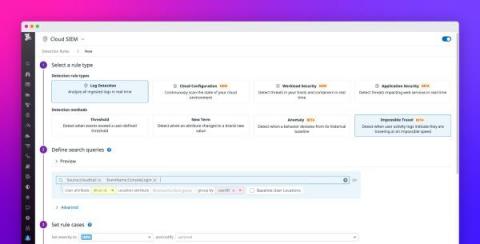
Detect suspicious login activity with impossible travel detection rules
Many modern applications are regularly accessed by countless users from all over the world, which makes it difficult to identify anomalous patterns in login activity indicative of a security breach. This challenge is compounded by the fact that people travel often and regularly access their accounts from new locations. To detect this common attack vector, the Datadog Cloud SIEM now provides the impossible travel detection rule type which helps you spot suspicious logins with confidence.
It's Easier Than You Think: Gaining Visibility Into SaaS Apps To Secure Your Data
Software-as-a-Service (SaaS) apps have become essential to how most of us run our organizations and stay productive — especially over the last two years. On any given day, you’re likely messaging colleagues using Slack or Teams, sharing files with partners from Google Drive or Microsoft SharePoint, or working in Workday or Salesforce to perform an HR- or sales-related business process.
How Nightfall is building the next generation of DLP
The current wave of digital transformation that has brought more and more businesses online has also introduced an unwelcome side effect: the surface area for attacks has ballooned. As individuals and businesses migrated their sensitive transactions into cloud applications, cloud service providers became responsible for providing high-fidelity data security.