Going beyond the standard: Announcing the State of Trust Report 2024 and VantaCon agenda
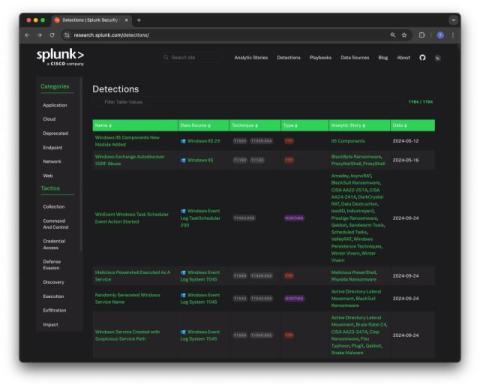
Building and scaling trust has become more difficult for organizations of all sizes. With more reliance on third-party vendors and AI technologies, security leaders face an increasingly complex threat landscape. However, many teams are left to manage this complicated landscape with screenshots, spreadsheets, and legacy solutions that rely on manual updates and limit them to point-in-time visibility into their security posture.