Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Geeks + Gurus - Adopting DevSecOps
Adi Sharabani, Snyk CTO On Adapting to Change: The Future of Security in a DevSecOps World
JFrog Presents: Triple Therapy for your Dev, Sec AND Ops Teams
Is it ODD to Shift Left? Building Elite DevSecOps Performers
Tracking the transport of radioactive sources with blockchain
This week, Australian authorities recovered a tiny capsule, just 6mm x 8mm (0.24 x 0.31 inches) along a 900km section of Australia’s longest highway, the Great Northern Highway. The pea-sized capsule was a radiation gauge containing caesium-137, a radioactive material with a half-life of 30.05 years, that is used to measure the density and flow of materials in the mining, and oil and gas industries.
5 Advanced DevSecOps Techniques to Try in 2023
How to Bake Security into your CI/CD Pipeline
Quick Start Guide: Integrate Veracode in Your DevOps Pipeline
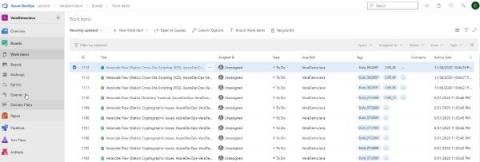
For today’s DevSecOps teams, the demands continue to intensify. Application portfolios and codebases continue to grow, while cyberattacks remain an ever-present danger. More than ever, it’s vital to ensure security gaps are identified and addressed with maximum speed and efficiency. In order to do this, you need to establish a continuous feedback loop on security threats, so you can realize optimized, sustained results – which is exactly how Veracode helps.