Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
What is PCI Compliance?
In today’s fast-moving and competitive marketplace, you can barely find any businesses and merchants that still haven’t adopted the use of credit cards for their services. More than a third of American cardholders use credit cards for their transactions on a monthly basis. With the rising prevalence of identity theft, over 1.1 billion personal records were exposed by data breaches and credit card fraud alone.
3 Steps To Remain PCI Compliant with your AWS Configuration
Becoming and staying PCI compliant both take a lot of work. Developers are often already swamped with an endless list of tasks, and adding PCI compliance can be overwhelming. Security awareness is one thing, but a set of requirements is entirely different. It means you have less freedom in how you wish to implement security in your application, and you must understand the requirements demanded by your organization.
Integrity Monitoring Use Cases: Compliance
The IT ecosystems of enterprises are highly dynamic. Typically, organizations react to this volatility by investing in asset discovery and Security Configuration Management (SCM). These core controls enable businesses to compile an inventory of authorized devices and monitor the configurations of those assets. In addition to managing changes to their infrastructure, organizations must also keep an eye on the changes made to essential files.
Open Source Intelligence
The term “open source” refers in particular to records this is publically available. A huge part of the internet cannot be found using major search engines. This is called as “Deep Web”. Deep Web is a mass of websites, databases, files, and more that cannot be indexed by Google, Bing, Yahoo, or any other search engine. Despite this, much of the content of the dark web can be considered open source because it is easily available to the public.
What is FIPS 140-2?
Securing the Digital Supply Chain Taslimm Q and Mike Machado!
Things You Should Know About Your Privacy Online
Surveillance is becoming an increasingly standard component of modern life, posing a threat to the idea that people have a right to privacy. In many situations, we unwittingly provide companies with information about our preferences, routines, and interests. In this age of digital era, you must not rely on evolving surveillance regulations and vendors to keep your personal information and security intact.
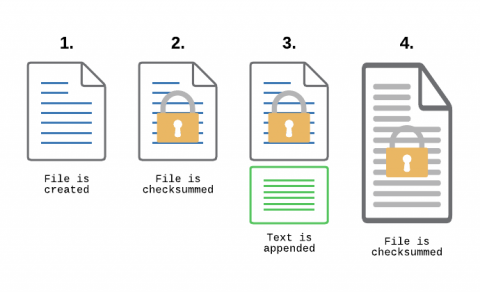
Monitoring Transaction Log Files for PCI compliance
File Integrity Monitoring, aka as FIM, is a must-have feature for anyone in charge of security. With FIM, one can detect when a critical file, such as a file that belongs to the Operating System, or a key configuration file, is changed. In most cases, configuring FIM is straightforward: If the file changes then generate an alert.
CrowdStrike Enables Federal Departments and Agencies to Meet CISA Operational Directive 23-01
In support of the Executive Order on Improving the Nation’s Cybersecurity, the Cybersecurity and Infrastructure Security Agency (CISA) recently published a Binding Operational Directive (BOD) 23-01, designed to improve cybersecurity for the Federal Civilian Executive Branch (FCEB) enterprise and their respective unclassified assets.