Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
How Snyk is normalizing authentication strategies with Gloo Edge
Snyk supports multiple authentication (authN) strategies on its APIs. Historically, API keys have been the primary form of authN, but more recently we introduced support for authN using signed JWTs produced as a result of an OAuth integration. This is currently in use by both our AWS CodePipeline and Bitbucket integrations. In the beginning, Snyk began with a hub and spoke architecture with a central monolith making authN decisions.
Are You Prepared for the Surge in Ransomware?
Incidents of ransomware have been increasing and evolving steadily for years as financially motivated adversaries shift tactics when one is no longer profitable. Unfortunately, many organizations haven’t been able to adapt their security operations to keep up. Back in 2019, 60% of organizations told ESG that they experienced a ransomware attack that year, with 29% reporting that attacks happened at least on a weekly basis.
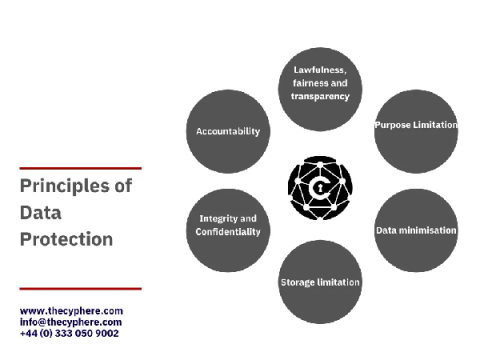
The 8 principles of The Data Protection Act & GDPR
The Data Protection Act 2018 is the legislation enforced by the Information Commissioner’s Office (ICO), UK, to protect personal data processing and data stored on the computer, digital media, or paper filing systems.
OWASP Mobile Top 10 Security Vulnerabilities and Attack Prevention
Far from the days of just phone calls and text messages, mobile apps have captured our attention with efficient experiences that keep us connected to friends, family members, coworkers. It’s all at your fingertips via these amazing apps- anywhere in the world! This blog post takes you through the OWASP mobile top 10 security risks, attack scenarios from OWASP and risk remediations that help cybercriminals get their hands on sensitive data.
Sysdig and Apolicy join forces to help customers secure Infrastructure As Code and automate remediation
Today, we announced that Sysdig is acquiring Apolicy to enable our customers to secure their infrastructure as code. I could not be more excited because the innovation that Apolicy brings to bear is unique and highly differentiated, allowing customers to strengthen their Kubernetes and cloud security and compliance by leveraging policy as code and automated remediation workflows that close the gap from source to production.
July 2021 Netskope Cloud and Threat Report
The July 2021 Netskope Cloud and Threat Report is the latest installment of our research analyzing critical trends in enterprise cloud use, cloud-enabled threats, and cloud data transfers. Enterprise cloud usage continues to rise, driven by collaboration and consumer apps, a continuation of a trend that started at the beginning of the COVID-19 pandemic and continues through today, as 70% of users on the Netskope Security Cloud continue to work remotely. At the same time, attackers continu