Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
5 ways to protect critical healthcare infrastructure from cyberattacks
Picture this. You’re an administrator in charge of providing basic amenities and day-to-day needs across 1,000 beds in an urban multispecialty hospital. One fine morning, you notice that all the patients’ bedside monitoring systems (the computer-like devices that display patient vitals like heartbeat and blood pressure) have stopped functioning, leaving doctors and nurses in the dark.
The ultimate guide to Cyber risk management
This blog was written by an independent guest blogger. Ambitious information security experts serve as a critical part of cyber risk management. The corporation is responsible for structuring IT and information security activities to protect its data resources, such as hardware, software, and procedures. To stay competitive, enterprises must design and establish secure environments that retain confidentiality and privacy while also ensuring the integrity of corporate information.
Sysdig Secure - When cloud provider security services are not enough
The benefits of cloud computing are causing the adoption of cloud services by companies of all sizes to increase each year. The reduction of operating costs, time to market, ease of use, and reliability are some of the most significant benefits. However, the shared responsibility model must be taken into consideration. Cloud breaches are already everywhere and it doesn’t look like they’re going to slow down anytime soon.
Fun with ciphers in copycat Wordles
Here at Snyk, we spend a lot of time researching vulnerabilities. We do that because there are a lot of other folks out there researching new ways to break into apps and systems. We’re often putting on our “grey hats” to think like a malicious hacker. I regularly view-source, look at network traffic and eyeball query strings. One such delicious little query string caught my attention this week on one of the many copycat Wordle sites.
What is a Botnet Attack? 5 Ways to Prevent It
A botnet is a cluster of machines that are infected with malware, enabling hackers to control them and unleash a string of attacks. Most commonly, botnets come in the form of distributed denial of service (DDoS) attacks, and recently the Microsoft Azure DDoS Protection team reported a 25% increase in these attacks when compared to the first half of 2021. Recent advances in technology have opened up a world of new opportunities for both consumers and businesses.
A Malicious Package Found Stealing AWS AIM data on npm has Similarities To Capital One Hack
In the latter part of December 2021, WhiteSource Diffend detected the new release of a package called @maui-mf/app-auth. This package used a vector of attack that was similar to the server side request forgery (SSRF) attack against Capital One in 2019, in which a server was tricked into executing commands on behalf of a remote user, thereby enabling the user to treat the server as a proxy for requests and gain access to non-public endpoints.
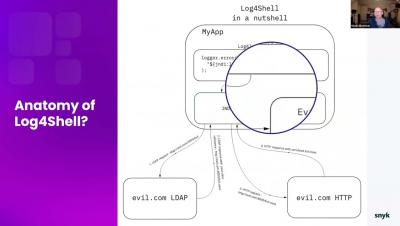
Log4Shell Live Hack: A Hands-on, Actionable Fix Guide
Forward Fix: Minimize Downtime with ServiceNow Integration
NewEdge, You've Come a Long Way Baby
Just over three years ago, Joe DePalo joined Netskope as Senior Vice President of Platform Engineering. He had most recently led the infrastructure design and build-out at AWS, the world’s largest public cloud, and prior to that, engineering and operations for one of the largest content delivery networks (CDNs) at Limelight Networks.
Cloud Threats Memo: New Malicious Campaign Using GitHub for Command and Control
State-sponsored threat actors continue to exploit legitimate cloud services. In their latest campaign, uncovered by Malwarebytes during January 2022, the North Korean group Lazarus (AKA HIDDEN COBRA) has been carrying out spear phishing attacks, delivering a malicious document masquerading as a job opportunity from Lockheed Martin (37% of malware is now delivered via Office documents).