Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Charts - Pie
The 3G network shutdown impacts more than just phones
As you have probably heard, 3G is phasing out. On February 22, AT&T shut down its 3G network. T-Mobile Sprint will retire its 3G network next week on March 31, 2022. Verizon, the last of the pack, will retire 3G by the end of 2022. What does this mean for your business and your security? The obvious answer is that older phones should be replaced as soon as possible, but the 3G shutdown’s impact will reach beyond phones, and that reach may affect your organization’s security.
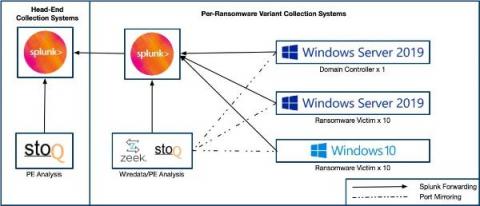
Gone in 52 Seconds...and 42 Minutes: A Comparative Analysis of Ransomware Encryption Speed
Do you feel like every other cybersecurity news story mentioned ransomware in 2021? Does it feel like you can’t turn on a cybersecurity podcast and not hear the “R” word? We feel the same way, and as a cybersecurity vendor, we felt that we should also contribute to the noise. :-) But we did want to try and do something different.
CrowdStrike Named a Strong Performer in 2022 Forrester Wave for Cloud Workload Security
“In its current CWS offering, the vendor has great CSPM capabilities for Azure, including detecting overprivileged admins and enforcing storage least privilege and encryption, virtual machine, and network policy controls.” – The Forrester Wave™: Cloud Workload Security, Q1 2022 CrowdStrike is excited to announce we have been named a “Strong Performer” in The Forrester Wave:™ Cloud Workload Security, Q1 2022.
Falcon OverWatch Threat Hunting Contributes to Seamless Protection Against Novel BlackCat Attack
In an effort to stay ahead of improvements in automated detections and preventions, adversary groups continually look to new tactics, techniques and procedures (TTPs), and new tooling to progress their mission objectives. One group — known as BlackCat/ALPHV — has taken the sophisticated approach of developing their tooling from the ground up, using newer, more secure languages like Rust and highly customized configuration options per victim.
Create an ethics-by-design approach for data
Our VP for Data Ethics & Governance, Sophie Chase-Borthwick, was recently part of a panel – the PICCASO Special Interest Group. Sophie joined William Malcolm (Privacy Legal Director at Google), Radha Gohil (Data Ethics Strategy Lead at Shell), and Anne Woodley (Security Specialist at Microsoft) in untangling what data ethics actually means and how best to support it. Here we look at this in more detail.
The Business Value of Security Service Edge (SSE) and the SASE and Zero Trust Journey
I’m not big on acronyms or buzzwords. Like many executives, my eyes glaze over when I’m being prospected with an alphabet soup of technology terms I supposedly “need” to care about. So why, then, does the title of this article include Security Service Edge (SSE), Secure Access Service Edge (SASE), and Zero Trust? Despite our justified disdain for acronyms, the ideas behind these terms hold genuine importance for business leaders.