Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
SEC's Proposed Disclosure Amendments: Are You Impacted?
On March 9, 2022, the Securities and Exchange Commission (SEC) announced proposed rules and amendments to enhance and standardize disclosures regarding cybersecurity risk management, strategy, governance, and incident reporting. These proposed amendments impact all public companies subject to the reporting requirements of the Security Exchange Act of 1934. To summarize this proposal and learn how to successfully prepare for them, read on.
LimaCharlie announces sponsorship of the Intel Owl open source project
Following our recent announcement about supporting the open source community, LimaCharlie is excited to share that we have decided to sponsor the IntelOwl project.
15 Ways to Protect Data with Digital Security Watermarks
Everyday business documents continue to be one of the biggest sources of data leakage. The Facebook leaks and WikiLeaks are prime examples of the damage such breaches can wreak. Even with the best security tools in place users seem to always be able to find a way to circumvent security. Or, as in most cases, accidentally share data with the wrong audience creating a security issue.
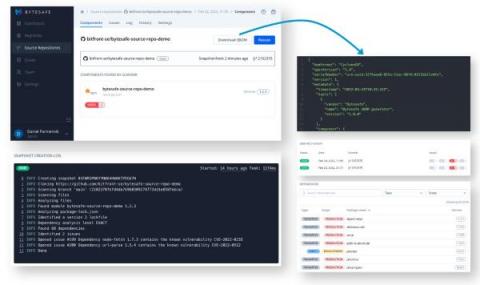
Export and Distribute SBOMs Directly From Your Git Repositories
Guest Blog by Daniel Parmenvik – CEO of bytesafe.dev For many, Software Bill of Materials (SBOMs) have changed from a manual list of assets for due diligence procedures to become an integral and automated part of software development. The ever increasing appetite for open-source software translates into a need to keep track of software assets (or open-source dependencies) for all applications, at any given point in time.
Protect Your iOS Keeper Vault with FIDO2 WebAuthn and Yubikey NFC
Tigera: Runtime Security for Cloud-Native Applications with eBPF
Tigera: Microsoft and Tigera: Hands-on AKS workshop - Implementing Zero-Trust Security for Containers
Tigera: Protecting modern cloud-native applications from network-based threats with runtime security
WatchGuard: Top Security Threats Worldwide: Q4 2021
7 vital security tips for enterprise cloud security administrators
Every organization has tons of sensitive information stored in the cloud. The unanticipated surge in remote work resulted in an increase in the amount of information stored in the cloud. According to TechJury, 67% of enterprise infrastructure is cloud-based. However, with organizations allowing employees to use both business and personal devices at work, the attack surface has expanded, increasing opportunities for threat actors to target vulnerable devices.