Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
Pentest People: Health and Wellness Support
Did you know that one in six people experience a mental health problem each year in the workplace? This statistic suggests that at least 16 people a year at Pentest People will suffer from a mental health condition.
CRLF Injection Attack - Explained
Web applications across the digital world are teeming with vulnerabilities increasingly equipped to defeat security mechanisms. Among them are injection attacks. We are aware of the many injection vulnerabilities present in a web application, for example, SQL injection, HTML injection, CRLF injection, cross-site scripting and many others. This article will discuss CRLF injection vulnerability in detail for web application security.
5 Cyber Hygiene Best Practices
4 lessons from 'Hack the Port' about 'critical infrastructure' cybersecurity
Cybersecurity leaders and practitioners recently gathered at Hack the Port in Ft. Lauderdale, Florida to discuss the evolving threats to ports – a key sector within the nation’s critical infrastructure – and how to better protect them.
eyeSight Admin API
kubectl Cheat Sheet
Kubectl is the default command-line tool for Kubernetes. It makes it easier to use the Kubernetes API and manipulate Kubernetes resources, allowing you to control Kubernetes clusters and run commands to deploy applications, manage cluster resources, and view logs. This guide will look at how best to integrate the most common and useful kubectl commands into your workflows, as well as provide some helpful tools for further optimization.
Secure application connectivity. Anywhere.
What's new in UpGuard // Cyber Vendor Risk Management Product Releases
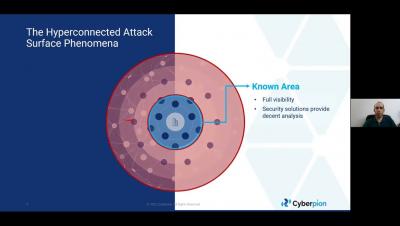
Hyperconnected External Attack Surface Protection
Weekly Cyber Security News 08/04/2022
A selection of this week’s more interesting vulnerability disclosures and cyber security news. For a daily selection see our twitter feed at #ionCube24. Oh come on, hard coded password? Really?