Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Latest posts
How to Protect Backups from Ransomware with NAKIVO's Malware Scan
Backups have become a primary target for ransomware. Hackers want to ensure that companies pay the ransom by not allowing them to recover their data independently. With NAKIVO Backup & Replication, you get several features (for example, immutable backup targets) to ensure that once created, a backup cannot be infected or corrupted with a new ransomware infection.
How We Prevented a Critical Jira Data Loss Incident (and So Can You)
As daily Jira users, the GitProtect Team experiences the platform’s pros and cons firsthand. A recent notification from Atlassian about data loss was a sharp reminder of digital fragility. Without GitProtect, our enterprise-grade backup solution, the loss could potentially turn into a critical data incident. Let’s see what happened and how we responded.
Is Shai-Hulud Back? Compromised Bitwarden CLI Contains a Self-Propagating npm Worm
Version 2026.4.0 of the widely-used @bitwarden/cli npm package (78,000 weekly downloads) has been identified as malicious. The package contains a sophisticated multi-stage credential theft worm that explicitly names itself "Shai-Hulud: The Third Coming", a direct callback to previous Shai-Hulud supply chain campaigns, and targets developer credentials including SSH keys, cloud secrets, and even MCP configuration files.
Falcon Cloud Security: Cloud Detection & Response for Google Cloud
CrowdStrike Cloud Detection & Response enables defenders to detect and stop attacks instantly, not just on workloads, but also in the cloud control plane.
From 24/7 On-Call to Holidays Off: AI SOC Automation Results from Three Security Teams
See how Torq harnesses AI in your SOC to detect, prioritize, and respond to threats faster. Request a Demo John White is the Field CISO for EMEA at Torq. A respected security executive with more than 20 years of leadership experience, John previously served as CISO at Virgin Atlantic, where he led a multi-year transformation deploying the Torq AI SOC Platform to modernize cyber operations.
13 Real-life Insider Threat Examples
While many organizations focus on external threat actors, insider threats are a significant risk that can devastate a business from within. Because these individuals have legitimate access to a company’s systems, their actions — whether motivated by financial gain or caused by human error — often bypass security controls. And the problem is only getting worse. According to the Ponemon Institute, insider attacks increased by 47% from 2023-25.
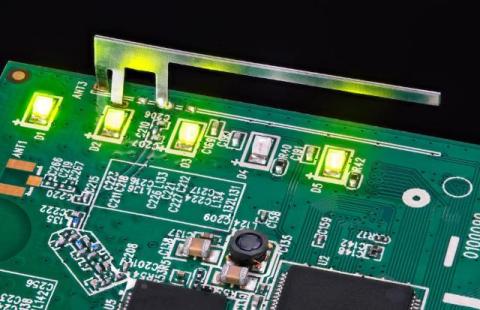
How PCB Layout Affects Wireless Performance
Wireless performance is often discussed as if it were determined mainly by the radio chip, antenna type, or communication protocol. Those factors do matter, but they do not tell the whole story. In real products, PCB layout often has just as much influence on wireless behavior as the module itself.
How Customer Support Outsourcing Helps Improve Cybersecurity: Best Companies in 2026
Cybersecurity breaches rarely start with a sophisticated exploit. More often, they start with a phone call, a chat session, or an email to customer support. Attackers probe support teams for account details, push agents to bypass identity checks, and use social engineering to extract credentials. According to a 2026 cybersecurity report by Medha Cloud, 63% of mid-market companies now outsource at least part of their security operations, and the managed security services market is projected to reach $46.4 billion in 2026. The pressure to both deliver exceptional customer experiences and maintain airtight security protocols has never been more intense.
AI Receptionists and the Expanding Attack Surface: What Security Teams Need to Know
AI receptionists are quickly becoming the front line of customer interaction, handling calls, capturing data, and integrating directly with business systems. But as organizations rush to adopt AI-powered customer service, a critical question is emerging: Are we securing these systems as rigorously as we deploy them? Because every AI receptionist isn't just a convenience, it's also a new attack surface.
How to Protect Your Images from Copyright Theft
In today's digital-first world, images are one of the most valuable assets a creator or publisher can own. Whether you're running a blog, managing a media site, or publishing news content, high-quality visuals drive engagement, improve SEO, and elevate credibility. But with that value comes a growing problem: copyright theft.