Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
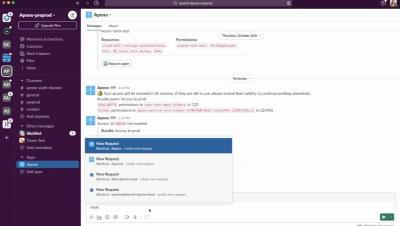
Two ways to request access to cloud resources on Slack - with Apono
Mitigating deepfake threats in the corporate world: A forensic approach
In an era where technology advances at breakneck speed, the corporate world finds itself facing an evolving and insidious threat: deepfakes. These synthetic media creations, powered by artificial intelligence (AI) algorithms, can convincingly manipulate audio, video, and even text - posing significant risks to businesses, their reputation, and their security. To safeguard against this emerging menace, a forensic approach is essential.
Handle secrets like API keys securely in javascript projects with environment variables
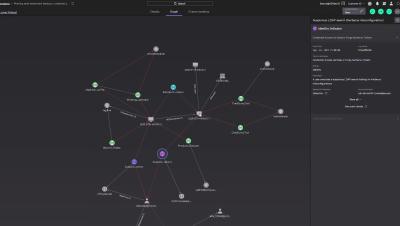
Announcing Ruby - your new Generative AI companion for Data Security
Say hello to Ruby, your new Generative AI companion for the Rubrik Security Cloud. Ruby is designed to simplify and automate cyber detection and recovery, something that IT and Security teams struggle with as cyber incidents are getting wildly frequent and the attacks are evolving quickly. A study by Rubrik Zero Labs revealed that 99% of IT and Security leaders were made aware of at least one incident, on average of once per week, in 2022.
Weather Forecast: Money Is Going to Rain from the Cloud
Since the start of Bitcoin in 2009, the popularity and prevalence of cryptocurrencies has exploded, resulting in a net worth of over $1 trillion that continues to grow. Cryptocurrency—held in virtual wallets—is obtained by users who purchase coins on a cryptocurrency exchange, receive coins as payment from someone else, or “mine” coins virtually themselves.
Falcon Platform Raptor Release
Importance of Encryption in Messaging Apps
A10 Networks Simplifies Google Cloud Platform Cloud Deployments
Securing APIs: Practical Steps to Protecting Your Software
In the dynamic world of software development, Application Programming Interfaces (APIs) serve as essential conduits, facilitating seamless interaction between software components. This intermediary interface not only streamlines development but also empowers software teams to reuse code. However, the increasing prevalence of APIs in modern business comes with security challenges.