Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Cloud Security and Compliance: A Smarter Approach to Keeping Your Head Above Water
When it comes to cloud security and compliance, it’s easy to feel like you’re drowning in a sea of regulations and requirements. But don’t worry; we’re all in the same boat! That’s why we’re thrilled to share our latest point-of-view (POV) paper, “Practical Cloud Security in the Era of Cybersecurity Regulation,” which is crafted with our deep industry expertise and experience.
From Doodles to Masterpieces: How AI Art Generators Transform Sketches into Art
Artificial Intelligence (AI) has permeated nearly every aspect of our lives, from powering virtual assistants to driving autonomous vehicles. However, one of the most intriguing applications of AI is in the realm of art generation. With the emergence of free AI art generators and background removers, individuals now have the power to transform simple doodles into stunning masterpieces with just a few clicks. In this article, we delve into the world of AI-generated art, exploring its capabilities, implications, and the creative freedom it offers to artists and enthusiasts alike.
AI, Platforms, Zero Trust, and Other Topics That Dominated RSA Conference 2024
Every year there’s quite a bit happening at the RSA Conference and no matter how hard you try, it can be difficult to take it all in. Between a sprawling showfloor with hundreds of vendors vying for attention, speaking sessions with experts from across the industry, private meetings with customers and prospects, plus social events in the evening, it’s understandable that you can come away with a bit of sensory overload.
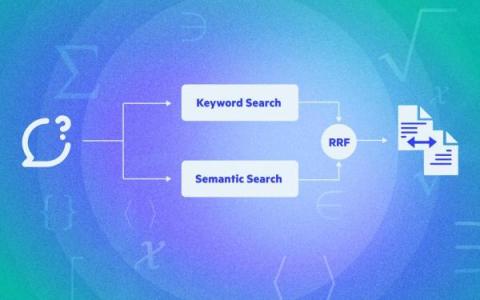
Part 1: How Egnyte Built its Turnkey Retrieval Augmented Generation Solution
The Egnyte platform houses a lot of data. To enable users to make the most of this asset, we need to help them efficiently retrieve information. Traditional search interfaces do a decent job of retrieving information directly related to query keywords, often presenting results in a list format without additional interpretation or synthesis.
FBI Warns of AI-Assisted Phishing Campaigns
The US Federal Bureau of Investigation’s (FBI’s) San Francisco division warns that threat actors are increasingly using AI tools to improve their social engineering attacks. “AI provides augmented and enhanced capabilities to schemes that attackers already use and increases cyber-attack speed, scale, and automation,” the FBI says.
What is System Management?
Every organization relies on technological systems to generate value. These systems work according to company policies that dictate their use. System management solutions allow IT leaders and their teams to enforce those policies in a consistent way across the organization.
Dani Grant (Jam.dev) | Fixing Bugs, Building a Company, and the Future of the Web
Dani Grant, co-founder of Jam.dev, talks about her company, how they are trying to fix the bug process for developers, and also discusses how Jam.dev uses Cloudflare. We also go over what a better internet for the future looks like, and the challenges and opportunities in the AI era.
How to stay ahead of AWS Lambda costs
Severless is excellent, right? Faster development and less infrastructure hassle – but those AWS Lambda costs can sneak up on you. Over 70% of AWS customers are using serverless now. Seems like everyone’s jumping on the serverless bandwagon – and for good reason. It speeds up development and cuts down on the nitty-gritty infrastructure stuff. All this is a developer’s dream in a lot of ways.
Enhancing AWS Security: Comprehensive Strategies for Robust Cyber Protection
With the rapid expansion of cloud computing, Amazon Web Services (AWS) has become a cornerstone for businesses seeking scalable and flexible IT solutions. However, this increased reliance on AWS has made it a prime target for cyber threats. Ensuring robust security measures within AWS environments is paramount to safeguarding sensitive data and maintaining business continuity.