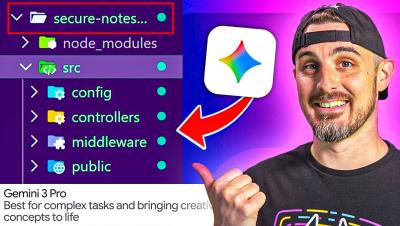
Google Gemini 3 Pro Builds an App with ONE PROMPT...
Google announced Gemini 3 Pro, which they tout as their most intelligent model yet that's best for complex tasks and bringing creative concepts to life. We're going to put this model to the test and see how good it is at fulfilling our prompt with a production ready app and the security of the code it produces.