Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
More Than a Tenth of Ransomware Attacks Now Involve Data Theft
Research into recent ransomware submissions revealed that more than a tenth of crypto-malware infections now involve some element of data theft. In the second quarter of 2020, ID Ransomware received 100,001 submissions of crypto-malware pertaining to attacks that had targeted organizations and government entities. Of those attacks, 11,642 involved the theft of victim data by their perpetrators. That’s over 11% of the attacks for that six-month period.
Smart Cache: Where Infrastructure Meets Content Intelligence at the Edge
Businesses have long relied on Egnyte’s hybrid technology for low-latency access to large files in bandwidth-constrained environments, and to ensure business continuity during internet outages. By syncing cloud content to a local storage device, hybrid architecture enables caching close to the user, which offers major benefits for customers who need cloud-scale connectivity with on-prem performance.
How to protect your IT infrastructure from a Maze ransomware attack
Pitney Bowes, a global package delivery giant, has been hit by a second ransomware attack in less than seven months, according to ZDNet. Those responsible for the attack have released screenshots portraying directory listings from inside the company’s network. What is Maze ransomware and what makes it so special?
DDoS attack prevention and protection explained
This blog was written by a third party author. Distributed denial of Service (DDoS) attacks stand as some of the most disruptive and costly cyberattacks that organizations face on a regular basis. Cyber criminals use DDoS attacks to make websites and other online services unavailable for legitimate use.
The damaging impact data breaches have on American society as a whole
This blog was written by an independent guest blogger. In the age of the internet where everyone has a mobile phone and multiple social media profiles, one phrase has become synonymous with doom and dread - data breach. It seems like these breaches have become a regular occurrence in modern society. Small businesses may be particularly susceptible to security hacks, but even large corporations are not immune.
Detectify achieves ISO 27001 Certification
STOCKHOLM — July 14th, 2020 — Detectify, the Sweden-born cybersecurity company that offers a website vulnerability scanner powered by Crowdsource – a network of ethical hackers, today announced that it has achieved the internationally recognized standard ISO/IEC 27001:2013 certification.
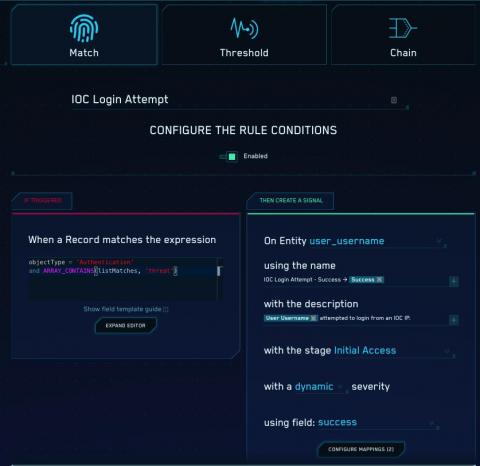
Cloud SIEM: Getting More Out of Your Threat Intelligence - 3 Use Cases for IOCs
Splunk Phantom Demo Video
Your 30-60-90 Day AppSec Plan
Your stakeholders have signed off on an application security program, you’ve selected a vendor … but now what? There is no detailed handbook or instruction manual for getting started because every organization is different. You need to formulate your own plan to make sure the program meets the individual needs of your organization.