Beyond the Endpoint: Why EDR/XDR Struggles in the Cloud
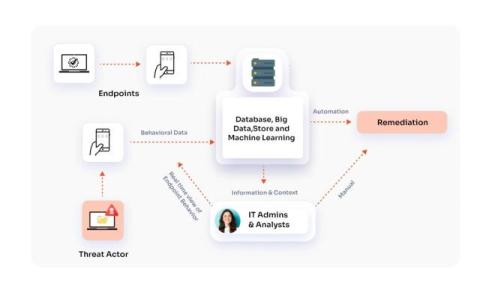
The cybersecurity landscape has dramatically shifted with the rise of cloud computing. While Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR) have proven valuable in protecting traditional endpoints, the cloud introduces a new set of challenges. This post examines why these solutions, rooted in endpoint-centric approaches, may fall short in the cloud, highlighting the need for a new generation of cloud protection strategies designed for SaaS, IaaS, and PaaS environments.