Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Splunk SOAR Feature Video: Install/Update Apps
Setting time ranges manually in Activeboards
Activeboards Calendars - Setting time ranges manually
How Network Segmentation Can Protect Supply Chains from Ransomware Attacks
Organizations can take various steps to protect their operational technology (OT) environments against digital threats. But some stand out more than others. In particular, network segmentation is described as “the first answer to insufficient ICS (Industrial Control System) cybersecurity.” Experts advocate zoning ICS assets to coordinate informational technology (IT) and OT environments effectively. That doesn’t always happen, however.
Data Security Explained: Challenges and Solutions
Data is the most valuable asset for any business. No matter what industry you are in, it’s critical to take care of your data, whether it is financial reports, healthcare records or a start-up business plan. Despite increased data protection regulation, data breach risks are growing. According to Capita, 80% of data breaches involve personally identifiable information at a cost of $150 per record.
Defending the Internet of Things from hackers and viruses
The 2010 Stuxnet malicious software attack on a uranium enrichment plant in Iran had all the twists and turns of a spy thriller. The plant was air gapped (not connected to the internet) so it couldn’t be targeted directly by an outsider. Instead, the attackers infected five of the plant’s partner organizations, hoping that an engineer from one of them would unknowingly introduce the malware to the network via a thumb drive.
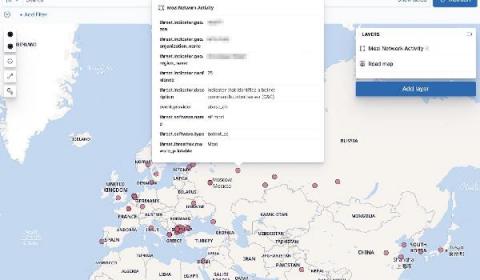
Collecting and operationalizing threat data from the Mozi botnet
Detecting and preventing malicious activity such as botnet attacks is a critical area of focus for threat intel analysts, security operators, and threat hunters. Taking up the Mozi botnet as a case study, this blog post demonstrates how to use open source tools, analytical processes, and the Elastic Stack to perform analysis and enrichment of collected data irrespective of the campaign.
Which Managed Kubernetes Is Right for Me?
Kubernetes helps with scaling, deploying, and managing containerized workloads, facilitating a faster deployment cycle and configuration management—all while providing improved access control.Kubernetes is also a CNCF project, meaning it’s cloud-native and can be easily deployed through any cloud provider. This blog will compare on-premises, or self-hosted,Kubernetes clusters to managed ones, as well as outline your options for Kubernetes in the cloud.
How to Securely Send Data to Your SIEM
Deploying a SIEM requires strategic planning. When deciding on a deployment, an organization must consider the level of risk it is willing to assume, what its security priorities are, and which use cases to implement. From there, your security operations team must thoughtfully identify their inputs — the data the SIEM solution will gather — before rolling out anything. Otherwise, you won’t obtain your desired outputs to identify high-fidelity alerts to act on.