Top 12 Privileged Access Management (PAM) Use Cases in 2026
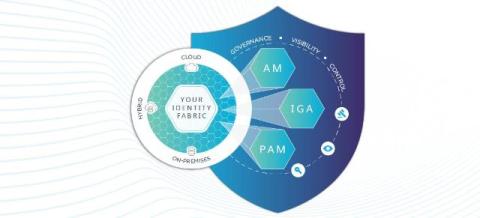
Privileged Access Management (PAM) is your organization's security control center for managing and monitoring high-level access to critical systems. Think of it as a sophisticated vault system that safeguards your most powerful administrative credentials while maintaining detailed audit trails of their usage. As we head into 2026, PAM has become crucial. Here's why: Cyberattacks are getting scarier and more complicated.