Security | Threat Detection | Cyberattacks | DevSecOps | Compliance
Reducing Splunk spend with LimaCharlie
Endpoints as well as applications such as AWS, Google Cloud, Office 365, 1Password, Slack, and thousands of others produce vast amounts of data. The volume of security data is growing, and this growth will continue for the foreseeable future. This, in turn, leads to several challenges: To solve these problems, many companies have adopted Splunk as their SIEM (security information and event management) platform.
Coffee Talk with SURGe: RSA, Karakurt, Apple Passwords, Confluence Zero-Day, Follina/MSDT Update
Graylog Security - The Affordable SIEM Alternative
CrowdStrike Introduces Humio for Falcon, Redefining Threat Hunting with Unparalleled Scale and Speed
Making a Business Case for the Right SIEM
Let’s admit it — switching to a new SIEM can be tough. And expensive. But even when it isn’t tough or expensive, it’s always scary.
Truth in Malvertising?
Splunk SURGe recently released a whitepaper, blog, and video that outline the encryption speeds of 10 different ransomware families. Early in our research, during the literature review phase, we came across another group that conducted a similar study on ransomware encryption speeds. Who was this group you ask? Well, it was actually one of the ransomware crews themselves.
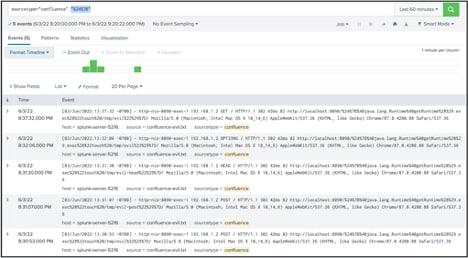
Atlassian Confluence Vulnerability CVE-2022-26134
If you want just to see how to find evidence of the Atlassian vulnerability in your Confluence systems, skip down to the “detections” sections. Otherwise, read on for a quick breakdown of what happened, how to detect it, and MITRE ATT&CK mappings.