How a volunteer-run wildfire site in Portugal stayed online during DDoS attacks
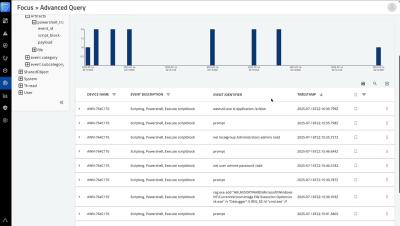
On July 31, 2025, just as Portugal entered the peak of another intense wildfire season, João Pina, also known as Tomahock, received an automated alert from Cloudflare. His volunteer-run project, fogos.pt, now a trusted source of real-time wildfire information for millions across Portugal, was under attack. One of the several alerts fogos.pt received related to the DDoS attack.