Lessons Learnt By An Agent Of Chaos From DevOps
What is Penetration Testing?
Penetration testing is one of the most efficient and straightforward methods to see how secure your systems are. Read our article to learn how penetration tests are done.
5 most common mobile phishing tactics
Phishing is one of the things that keeps CISOs up at night. Phishing attacks are effective and simple to launch, and used by financially motivated attackers as well as more targeted attacks. In the case of a targeted attack, it may harvest login credentials to gain access to corporate or personal resources. In fact, sometimes corporate access can be used to steal personal data, and vice versa.
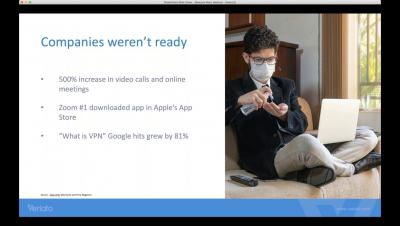
Effectively Managing The Shift To A Remote Workforce
PCI Compliance for Containers and Kubernetes
Open Source Analysis Extends Your Visibility
When we think of open source analysis, security is often the first thing that comes to mind. But open source analysis is so much more than just security. It gives you visibility into your codebase to help you understand and manage your open source components. In this blog, we’ll define open source analysis, look at why it’s important to your business, and describe the characteristics of an effective open source analysis framework.
Kubernetes Threat Intelligence: Detecting Domain Generation Algorithms (DGA)
The origin of Open Policy Agent and Rego
Why the cloud-native architecture required a new policy language I recently started a new series on the Open Policy Agent (OPA) blog on why Rego, OPA’s policy language, looks and behaves the way it does. The blog post dives into the core design principles for Rego, why they’re important, and how they’ve influenced the language. I hope it will help OPA users better understand the language, so they can more easily jump into creating policy of their own.
7 key steps to Zero Trust
This is part 3 of a 3 part blog series My last two blog entries provided some key elements of a Zero Trust Network (ZTN), which focused on the tenets of zero trust and how the confidence is gained for untrusted traffic and authorized on a continual basis. The comprehensive nature of Zero Trust can be a little overwhelming in a world of limited resources, time and budgets.