NormShield vs. SecurityScorecard Comparison
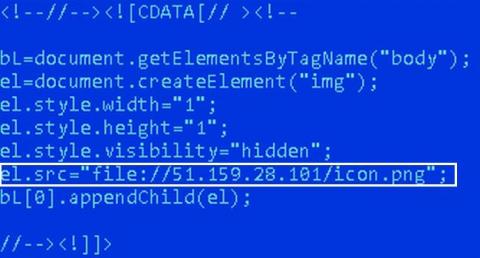
The average cost of a data breach is now nearly $4 million, and the unfortunate truth is third-parties are a significant source of cyber risk. These increasing costs are why cybersecurity vendor risk management (VRM) is a top priority for CISOs, Vice Presidents of Security, and other members of senior management, even at the Board level. In addition to financial costs, regulatory and reputational costs are increasing.