Elastic Security 101
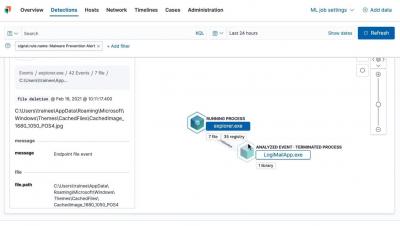
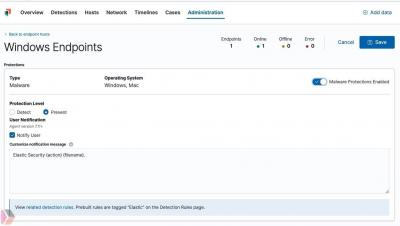
Elastic Security empowers analysts to collect data from multiple data source integrations, perform traditional SIEM functions, and take advantage of machine learning-based malware protection on the endpoint. Analysts can filter, group, and visualize data in real-time while performing automated threat detection across various security events and information. In this video, you’ll learn about the components that make up Elastic Security and what those components do to help you protect your data.