Corelight Smart PCAP
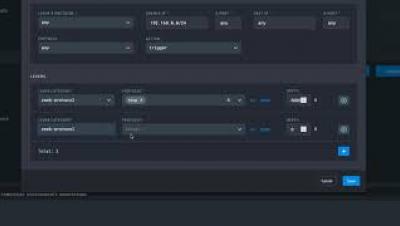
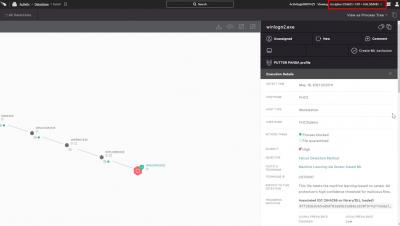
Security teams can save up to 10x the packet retention period at 50% the cost compared to full packet capture! Sounds too good to be true, right? It’s not! With powerful, yet easy-to-use pcap levers we let security teams capture just the packets needed for investigations, and correlate them with our alerts and logs, and make packets 1-click retrievable. With Smart PCAP you get months, not days' worth of packet visibility.